
 Well-known old school hacker and phone phreak John “Captain Crunch” Draper delineates the major milestones in the evolution of different types of hacking at CONFidence IT security event.
Well-known old school hacker and phone phreak John “Captain Crunch” Draper delineates the major milestones in the evolution of different types of hacking at CONFidence IT security event.
Hello everybody! I don’t know if you’ve heard of me or not, but I was the old school hacker back in the early 1970s, where my claim to fame was using the ‘Captain Crunch’ whistle to make free phone calls.
This is a ‘Captain Crunch’ whistle (see image below), and you glue up one of the holes, then you blow the whistle, and that whistle is the pitch that controlled the AT&T telephone switching system.
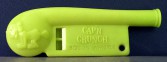
Let’s see, if I wanted to dial 234 I would just dial the numbers by repeatedly blowing the whistle that many times, and then that would make a free call. You would do that by calling an information number or 800 toll-free number, and blow the whistle in, and you hear a little chirp sound, and that indicates to you that you are actually connected to an internal trunk line that is a raw trunk line. This trunk line is not the same kind of line you as a subscriber would use; this line is nothing more than an internal trunk line. It’s like getting root access to the phone system.
Now I’m going to give you guys a little history of hacking as seen by an old school elder like myself, because when I grew up there were no personal computers.

Back in the day there was the IBM 360, and my exposure to IBM 360 was programming in Fortran using batch cards; and I’d have to wait about three hours to find the result of my program run, and more than likely I would find a mistake – forget a semicolon at the end of the statement or something – and had to resubmit the batch again and wait for another three hours. Well, that really kind of sucked.
So, the other systems, of course, are Ultrix and DEC. Ultrix is a form of Unix, and DEC is the PDP-8 and the PDP-11 at the time, and they offered timesharing services. There used to be a company called ‘Tymeshare’ whose services were also used back in the day.
The very first viruses were probably in the early 1970s. The virus was nothing more than a little thing, a little display that would come on the screen and say: “I’m the creeper, catch me if you can!” And the purpose of trying to solve the problem was trying to identify where that virus came from, and that was a challenge for hackers.
Let me talk a little bit about hacking: what the definition of hacking is. Hacking is not accessing a computer system illegally and hacking passwords. Hacking started long, long time ago when a program was modified to do one particular function, and what you did was you would then take this program and hack it into different little pieces, recombine them and re-put them together into another program that either can make this program perform better or do something totally, completely different.
Only large universities would have computers back in the day. So, if you were a student, and if you were taking the right kind of courses, and if you had a cool instructor, your instructor would probably give you an account on your college computer back then.

Then came mini-computers. Typical cost for mini-computers was anywhere between $75,000 to $500,000, depending. Most universities had them; large companies would have them. The exception was Alex Kamradt: he happened to have a BTI in his garage running an HP 2100 mini-computer, and it could only run Basic. The cost was $120,000; it had 16 ports on it and it only ran Basic.
A lot of pranks occurred back in the day too, where people would write programs to do strange things and to confuse the instructor. We’ll talk about some of these pranks later.
The Stanford AI lab had a ‘blue box’ program. This is a program that generates the multi-frequency tones, unlike what the 2600 Hz whistle did, that allowed you to be able to combine 2 out of 6 tones to create and to form a phone number. They would allow you to be able to have an opening tone, the number, and closing tone.

Now, when you’re accessing the telephone company at the trunk level, you have got either 3 digits, or 4 digits, 5 digits, 7 digits, 9 digits, 10 digits; and so you had to have a way of telling when you were done dialing the number, so you had to have an opening tone, the number, and closing tone.
The Alto system by the Xerox Palo Alto Research Center had a lot of basic stuff, and, in fact, that’s where the Mac graphic user interface came from – the Alto computer that was created at the Xerox Research Center.
Phone Phreaking 101
Who is a phone phreak? A phone phreak is a person, usually blind, because the only things that are in their lives are audio and what they can hear. They’ve got exceptionally good hearing. By hearing the clicks and the whistles, and the pops, and all the stuff in the background they can detect what we can’t do.
And that’s why they can do what they can do. They were able to dial a number, and just by listening they were able to hear the little multi-frequency tones in the background, so faint that the normal person can’t hear it. They figured out that there had to be a way to do that. So, after doing a little bit of social engineering at the telephone company office they would have the ability to figure out what those frequencies were.
And then they associated those frequencies with keys on the organ. And then, to dial a number they simply played two notes at a time in different combinations to make the number. And this is how the cost of phone calls had gone way, way down.
Back in the day, to make a long-distance they used to advertise: “Make a 3-minute call for $1”, in the US. And that was a big thing the AT&T kind of bragged about. So, calls were typically around 30 cents/minute back in the day. And now, you know, a few cents a minute to make a phone call is what you can do. So, you know, this is amazing how the cost of calls has really gone down.
Methods the Old-School Phreakers Used
Now, some of the methods that the old-school phreakers used. One of them is called the mute box. What the mute box does is it takes a 2.7 kilohms resistor in series with the phone line, so that when the phone call comes in, you had a little button; you pushed the button really fast and that would stop the ringing tone but still leave the connection open. But there wouldn’t be enough current to cause the telephone to go off-hook, so therefore the billing equipment wouldn’t trigger.
This allows you to be able to receive phone calls for free to the person that’s calling you. So the person who’s calling you will not get billed for it. Why? Because you’re not picking up the phone. You are basically leaving the phone on-hook. But you’re listening to the audio, because the audio still can go through that 2.7 k resistor to the phone line.
The next thing which is very useful is called loop around numbers. Loop around numbers in the San Jose area always began with 0044 and 0045. If you dial the 0044 side, you get a high-pitch tone. It’s a 1000 Hz tone interrupted every 10 seconds. If somebody else were to call 0045 side, the two of them could get connected together and they could talk. Very useful when you want to kind of mask who your phone number was. In fact, that was how I actually got hold of Denny1. He gave me a loop around number. I called the operator, and she said: “That’s an internal test number, why should you be calling that number?”
He called me back about a month later and explained to me what loop arounds were, and I had to find out more, so I made an arrangement to meet Denny, and that was when I first learned all about how blue boxes worked.
The other thing is demonstrators. Back in the day the telephones were rotary dial. So they had to have a way of demonstrating how the new touch tone system would work. So, what they did was: you dialed a 7-digit number and it would answer with a dial tone, and you then could use your touch tone phone right next to that phone to show how fast you can dial a number; these are called demonstrator lines. Normally, these demonstrator lines are restricted to local calls only.
Yet another thing phone phreaks would use was party lines. There are 2 different kinds of party lines: one of them is if you call a busy number, like a radio station – you can actually talk between the busy beeps, and so you can give enough information out to get them to call you or something. It’s not very good to hear that constant beep all the time.
Other phone phreaks figured out that if you opened up the sleeve at an old step office, you could actually have a 10-party conference line. If you can take 10 numbers that aren’t used and you open up the sleeves in the wires, then you can actually make a conference call; usually that took social engineering because you had to call the telephone company switch office, you had to convince the guy that it’s ok and cool to bend the sleeve open to make it work.

Then there are blue boxes. Blue box is a multi-frequency device; it combines different tones; there are 700 Hz, 900 Hz, 1100 Hz, 1500 Hz, and 1700 Hz. They are odd frequencies, because that way they won’t interfere with each other. It’s quite a bit different than touch tones.
Then there are red boxes. Red boxes are the boxes used for making free calls from payphones. All it does is just emulate the sound that operator hears, with money going into the phone. They have the 3-coin payphones: you put in a nickel and it goes ‘ding’; you put in a dime and it goes ‘ding-ding’; you put in a quarter and it goes ‘gong’. And that’s what the operator hears, and that’s where she knows that you are putting money in the phone.
There’s actually a demonstration number in Vancouver, Canada; it’s a recording, you dial 604-11-21 and it goes: “five cents – ding, ten cents – ding-ding, quarter – gong”. And it just repeats it over and over again, it’s like an operator training tape. And these are some of the really cool things that we found kind of exploring the system. It wasn’t the idea of making free calls, it was the idea of hacking into the system, and that’s what made it really exciting.
Why Phone Phreaking Worked
Well, AT&T’s decision to use what they called ‘in-band signaling’ was their downfall, very bad idea. Because if you can use ‘in-band signaling’ and signal on the same wire pair that you’re talking on – my god, that’s like giving away the jewels to your system; it’s like giving root access to your computer. That’s not a very good idea.

Using this ‘in-band signaling’ was the 2600 Hz that I showed you with the ‘Captain Crunch’ whistle, but pulse dialing. Joe Engressia was the first phone phreak to actually use his mouth, not a Captain Crunch whistle, just his mouth to whistle a free call. Joe Engressia’s more recent name is Joybubbles. He has since passed away several years ago, but he was one of the very first phone phreaks. Now, there’s going to be a book out by Phil Lapsley called “Phone Phreaking” and it’s going to be coming out in the next few months, so be on the lookout for it.
What can you do with this power? You can do anything an operator can do, plus more. You can tap phone lines; you can access inter-trunking routing codes; you can reach ‘inward’ operators – these are operators in distant cities. Like, if I want to call, let’s say, New York, NJ I call 201-121: 201 is the area code for New Jersey, 121 is the ‘inward’ operator for New Jersey, she’ll answer the phone: “New Jersey”, and usually these operators will just connect you without any questions asked, because in order for you to actually reach that operator you have to be an operator yourself.
So, these inter-trunking routing codes are always three codes: like, in the 209 area code there’s a number of different cities: there’s Stockton, there’s Modesto, and there’s a few other cities. Stockton would be, like, 042, so you’re going to first dial 209 area code, so you dial 209-042-121. And that’s how you can reach ‘inward’ operators. You can manually route the calls by stacking those numbers together, so you can do 209-042-044-042-044-042-044, and you can keep looping around over and over again, and that’s how you can stack tandems.
Arpa Net – Early Days
Now let’s go back a little bit to computing. Back in the mid-1960s and the late 1970s there was the Arpa Net. The Arpa Net was the military’s way of getting access to computers during war time, when all the universities and stuff like that had their computers tied together on what they called TIPs – Terminal Interface Processors.
Those TIPs allowed you to be able to access computers from different colleges and universities. MIT had one, Stanford had one, and all these large universities had their own computers. Back in the day every Arpa Net host had a guest account, and you could go in, you could write programs, like chess programs, the green/black chess programs.
One time I took MIT with 2 terminals, I pitted MIT against Stanford in the game of chess, so I would duplicate the move that MIT made over to Stanford, and when Stanford made a move I would duplicate that over there. By the way, MIT won.
Most hosts had guest accounts, they had very little storage, just enough storage for you to be able to run and test a few programs. Most allowed you to play computer games and offered academic related programs, for instance, to help you with your math and something like that. And that was called the ‘Gentlemen’s Systems’.
Back in the day, normally, nobody had computer terminals. If you happened to have a computer room in the college or something like that, you could get on the Arpa Net and you could dial local Arpa TIP, dial ‘L+space+39’ and log in, you’ll get another prompt, and that prompt is MIT or whatever it happens to be, depending on the code.
Early BBS Days

Now let’s bring ourselves to the early 1980s. In the early 1980s DC Hayes came out with the first consumer product modem. It was 1200 baud, and this modem would basically allow you to access computers remotely through a phone line: by calling up the phone number, you get the high-pitched screech, you get connected to the computer.
Normally, BBS systems were used at that point. FidoNet was one of the more popular BBS systems, written by Tom Jennings. I see Tom quite a bit in the clubs in LA by the way, he’s still around. He’s not very active anymore in the computing industry, he’s getting on with his age like me.
A lot of illegal hacking methods were discussed at this time. Back in the BBS systems they’d publish usernames and passwords. And one of the most famous ones was the 8BBS. 8BBS stands for PDP-8; BBS is a bulletin board system running on a PDP-8 system. The owner of that thing was called Bernard Klaat; he got busted for running his PDP-8 BBS system. Of course he had more than one user on the PDP-8, but you only can have one user on your Apple, or on your Atari, or your Windows, or whatever you happen to be running.
Online Systems
Back in the day there was Compuserve – they were the most expensive, I think they were like $12 an hour. There was another system called BIX. For three months they had free accounts. You could just give yourself a free account on BIX and off you go, and then they started charging about $5 an hour after that, and their usage dropped from amazing down to about 1/100th of what they were using before.
There was Delphi and another online system which was very, very popular, called the WELL. WELL stands for the Whole Earth ‘Lectronic Link. These are the people with Stewart Brand. Stewart Brand and a lot of the people down in the Palo Alto area came out with the book called “What to Do After You Hit Return” – a very popular book for beginning students. There was also AOL, and of course there were many others.
 Okay, what I’d like to do now is tell a few stories about some of the stuff that we did, because I kind of wanted to save the best for last. One of the things that I really wanted to point out is that there was no 800 directory, a directory of 800 numbers. So, in order for you to find 800 number, the only way you can do that is to watch the ads on TV, newspapers, or whatever.
Okay, what I’d like to do now is tell a few stories about some of the stuff that we did, because I kind of wanted to save the best for last. One of the things that I really wanted to point out is that there was no 800 directory, a directory of 800 numbers. So, in order for you to find 800 number, the only way you can do that is to watch the ads on TV, newspapers, or whatever.
And so, what you’ll need to do is basically figure out how you can find 800 numbers. There were a lot of independent companies that were giving away 800 directories.
Well, I said to myself: “I bet Washington, D.C. must have some really interesting 800 numbers.” So I decided to scan every possible 800 number in Washington, D.C. It turns out that Washington, D.C. 800 prefix is 800-424; that translates into 202 area code. And so, all I did was I would just dial 800-424-0000 thru 9999.
I would skip every 10 numbers because of the recording that says: “We’re sorry, your call cannot be completed as dial. This is a recording 2022.” That means the entire bank of 10 numbers is not valid. So, therefore, why should I go through every 10 of those numbers? So I skipped by tens: 0010, 0020, 0030, 0040, and then until I find a working number. If I got a recording that says: “We’re sorry, the number you dialed is not a working number,” then that must mean the entire bank of 10 numbers is a valid bank of numbers to use, so then we’d skip by 1’s.
And so, I found out that 800-424-933-7 went into a very interesting individual. The person who I called at that number was extremely rude to me. Why would anybody who would want you to call them and pay for your call not want to talk to you?
So, therefore that number had to be something special. I wrote this down in my little special book and later on, a week or so later, I went back to that number and I said: “Yeah, I should figure out where that number comes from.”
So I called the number again and this time I said: “Hi, this is White Plains for a trunk testing, AT&T long lines division. Who have we reached?” And the person says: “You’ve reached the White House, sir; this is the CIA crisis hotline you’ve called.” I responded: “Oh, sir, we’ll get it fixed right away for you; we’re having some translation difficulties. Thank you very much,” and I hung up. Okay, I wrote down: “White House CIA crisis hotline number.”
Now, a lot of telephone phreaks get together at parties and stuff like that. They like to trade information. One particular phone phreak had this really amazing conference number and I just had to have it. So he says: “What have you got to give away?” I say: “Well, I can give you the CIA crisis hotline to the White House,” and he said: “You have what?” I said: “Yeah, I’ve got the CIA crisis hotline number to the White House, you want it?” He says “Yeah!”
Okay, after I found out the crisis hotline number, the next thing I had to do is I had to find out where’s the 202 area code it came in. It turns out that 202-456-9337 happened to be a regular 10-digit number. So, back in the day they had ‘auto verify’, which meant that if I could get directly into the 202 trunk line, if dialed KP 052-252-9337*, I get ‘click’, ‘plop’ and then I get the scrambled noise.
I flash it with 2600 and it goes ‘beep’ – and it just clears away and I can hear the conversation on that number now. So I’m sitting there listening to the conversation on that number, and then I hear the conversation that says: “Olympus, please,” and then the guy says: “One moment, sir,” and I swear, the guy that came on the line was President Nixon. I wrote down: “Olympus, President Nixon.” Then I gave that to him as well.
Okay, so what happened was my friend Adam grabbed the phone from me and then he says: “I know what I’m going to do.” He called the number up, but I said: “You really don’t want to call that number directly; you really want to call that number in stack of a few trunks.”
So, what we did was we stacked a few trunks so that it would be harder for them to trace us back, because we knew that this could really result in somebody getting into trouble. So, Adam says: “Olympus, please” – “One moment, sir”, and Olympus came on the line and says: “Olympus.” He says: “Sir, we have a national crisis on our hands here in Los Angeles. Sir, we’re out of toilet paper,” and we hung up.
The idea of that was the fact you could do that kind of thing back then. I believe it was 1974-1975, this was just during the time that Nixon was having all this Watergate stuff going on. And I think he got kicked out of office soon afterwards. But that at least was what we did.
A couple of other pranks that we did had to do with dialing old funky step-by-step exchange, these are the old switches. Well, Santa Barbara was operated and controlled not by Pacific Telephone Company which is in California. It was operated by General Telephone Company which is a totally different private telephone company. And they’re also using 2600 signaling and trunking for the lines.
So, if you were to call into Santa Barbara – I had to dial into Santa Barbara with 2 phone lines exactly at the same time – and if you picked it just right, maybe 1 in about 50 tries, you get this high-pitched scratch, and all of a sudden just silence, and then you get ‘burp’, ring comes in: “Hello, is Maple there?” – “You got the wrong number, lady,” and then we hung up.
Oh, this is interesting; we’re intercepting calls going into Santa Barbara. So we started saying: “Oh, why don’t we do this?” We said: “We know what we can do.” The next call that came in was: “Sir, this is The National Guard, Santa Barbara had a nuclear accident. We are not accepting calls into Santa Barbara at the time. Please call back later.”
After a while, more and more calls started coming in, people started realizing and words got spread around, and then the press started calling and it started just getting pandemonium, because we were on the primary selector group for all trunk lines going into Santa Barbara.
We did this with two phone lines by just simply causing what is called a ‘glare condition’. A ‘glare condition’ is where you’ve got 2 trunks looking at each other, and they’re glaring. This guy is waiting for this guy to do something, this guy is waiting for this guy to do something, so they’re sitting there staring at each other, figuring out what they’re going to do.
But as a result of that process, calls coming in would show up as on-hook, which meant that the numbers were not engaged. But all those calls that were coming into that primary selector group wouldn’t jump over to the next line, it wouldn’t work that way. It just jammed up the lines and then the calls just started piling in. And so, when we told them about the nuclear bomb hoax, it wound up in the LA Times.
And there were also some cases when I was with Steve Wozniak. Steve Wozniak got these little radio transmitters for 160 MHz. And if you go up to a drive-thru like McDonald’s, you drive into McDonald’s, you see this clown Ronald McDonald who says something in his little speaker: “May I take your order please?”
And that was over 150-160 MHz frequency. So, Steve was sitting in his car, way in the back there, watching these people drive in, and he’d say: “May I have your order please?”, and then they’ll take the order and they’ll come back, and he’d say: “Lady, you’re too fat, I’m ordering a veggie burger for you instead”.
Anyway, that’s it for my presentation. Thank you!





























Its interesting.
I know who was the first person to use the whistle. I was a little kid and made a call to a friend and accidentally called a wrong number from Hawaii to California . I finished eating breakfast and was blowing the whistle . I talked to some guy for about 4 minutes .I told him what happen and how I did it . I was maybe 11 or 12 years old . The guy said his was going out to buy one right away . I blew the whistle with him on the line to show how I made the call and I called a foreign country by accident.
Captain Crunch and Mitnick were my heros. I would have loved to storm PACBell ot NYBell for the book with them os at least the Captain. What an amazing time we cam to age in. Full of possibilities and fellow hackers. and yes, I had a whistle and used it for my grandparents and father to speak to their family in Italia. I was first gen Ital-American.
cool.
l john draper is the best.
nice