aestetix, a researcher of online identity issues and one of the enthusiasts that created the Nym Rights group, gave a great talk at Shmoocon 2013 event entitled “Beyond Nymwars” highlighting the various facets of online names use within the identity-related context.
Before I start I just want to thank everyone at Shmoocon, all the Shmoocon staff for putting this together, because conferences are hard to do, so can we get a big round of applause for all of them? And if anybody here is not having a good time, can you raise your hand? Ok, that guy needs to be taken out and shot. Alright, fair enough, smack him on the head with a beer bottle. That’s right, cool.
Welcome to Beyond Nymwars and thank you all for coming to the talk. I will get into a whole bunch of stuff, and, by the way, I have a lot of material; I’m going to do my best to keep it within time, and if I run out of time with no time for questions, I’ll probably be up in the lobby, so feel free to come up and ask me things later. And if I seem to gloss over some parts of it – that’s why, feel free to come up and ask follow-up questions, please, because it’s becoming a life passion for me, as we’ll see.
I want to open up with a couple of quick questions. First: how many people here have a name? What about you, guys, you’re not raising your hands, you don’t have names? So, my next question: who here does not have a name? What is this, Schrödinger’s cat or something? Come on! You’re all numbers, ok. My third question: does anyone here have a name that they’ve given themselves? Half the crowd, ok, more than I thought.
By the way, this is my own artwork (see right-hand image): I spent about an hour in Photoshop learning a bunch of different things, so if it sucks, blame me. This is a juxtapose of Darth Vader, the Evil Empire and Anonymous. By the way, I assume everyone here heard of Anonymous. Anybody who hasn’t? They’re anonymous, yeah, exactly.
Ok, so here is another entity (left-hand image): I’m curious if anyone has heard of Google. There’s a lot of great things about Google, and no, this talk is not bragging about Google completely, just so you know. There’s a lot of great things that they do, and one of the things they did, actually, it was 2 years ago, I guess, Summer, July of 2011 – they introduced this thing called Google+. Has everyone heard of it, Google+? Anyone who hasn’t? It’s a unifying social network competing with Facebook, all this other stuff.
And Google+ seemed to be an answer to all kinds of things. I hate Facebook, I don’t know about you guys, and I wanted to see something come along and take down Facebook. I was really excited, I was advocating that all these people use it, and then this happened to me. I don’t know if you can see it on the screen (see right-hand image), but it basically says: “After reviewing your profile we determined that the name you provided violates our Community Standards”, that’s what they call it. And this is how I discovered this thing called the “Real Names Policy”.
By the way, just to show how together Google was at that time – the link, it was a dead link, it was a 404. Figures, right? That’s kind of where I got the inspiration and started looking at all these different facets of identity and where things break, where they work, and maybe try to rally people and have discussions about it.
I don’t know that I necessarily have any answers for you, guys, but I can share things that I’ve learned, my experiences that I’ve had, and as you see up in the upper right corner, I’ve helped form a group called: “Nym Rights”, where we want to get people to discuss this stuff and see what does identity mean to anyone of you. That’s kind of the point of all this.
So, the thesis statements of this talk:
2. This is something that’s become a real passion of mine – there’s no such thing as a “real” name. Legal names – sure; real name, I think, is actually a dangerous concept.
3. As I’ll show with evidence, imposing a singular identity is not only harmful – it doesn’t work.
There’s kind of an institutional effort to push people into a single name right now, and there’s some issues they I have with it. In any case, has anyone here heard of NSTIC? A few people, ok, great.
So, NSTIC is known as the National Strategy for Trusted Identities in Cyberspace. And it’s kind of this initiative by the Obama administration to try to address the challenges that we’re looking at right now. How many people know that passwords are totally broken? Has anybody here been compromised because of a weak password? Ok, you guys are honest, that’s good.
One of the things that we’ve seen, especially in the last two years with Anonymous and LulzSec and all the password dumps, is that classically we’ve had tools that do password brute-forcing and such, but now, with like 2 or 3 million dumps of passwords for emails and such, the people who are writing these tools actually have real-life passwords that they can work from and construct patterns from and figure out how people actually create their passwords. For example, how many of you know somebody who has a password that’s their dog’s name or something?
Right! And there’s all kinds of other issues: identity theft and things like that. In fact, NSTIC has a whole bunch of different working groups, or committees, as they call them. They address security, privacy management, outreach, things like that. I came along and I’m like: “Well, this looks really interesting, we should make sure that they know about nyms and nym rights and all this other stuff, and names, and how they work”, because it turned out they hadn’t really address all of that.
So there was a plenary that happened a couple of weeks ago: I went there on the 5th through 7th of February, and we had a 4-hour-long discussion about nym rights and how names could work into this government initiative, because…how many people see that and think like: “Fucking scary real ID or, you know, tracking and stuff like that?” How many get freaked out when they see that? All of you need to join and make sure that doesn’t happen. We’ll get into that more in a second.
By the way, I am going to cover some basic myths of identity and things that people think about pseudonymous and anonymous identities. All of those myths that I will cover were things that were brought up in the discussion, so it’s not like I’m bringing up strongman because it’s convenient to make my points. I had to make all of these points at the plenary a couple of weeks ago with the people who are in charge of trying to figure this out for the government and the private sector and everything else. So, just keep that in mind.
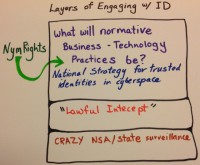
So, where does Nym Rights fit in NSTIC? (see rigt-hand image) I like to call these the threat levels: you got the top threat level, which is – I guess the threat level at yellow, the super happy one, the green one, where you have where we fit in; we’re trying to have open discussions with governments and corporations and figure out how we can set things up to make sure that everyone’s prospective agency is respected.
And then you have the middle level there, the “Lawful Intercept” – NSA surveillance, things like that. And then you have the third level, that crazy NSA/state surveillance. So, the third level, aka Threat Level Red, whatever you want to call it, that is what a lot of people think of when they hear: “National Strategy for Trusted Identities in Cyberspace”. They hear “rigid horrible things in real ID and tracking and all this other stuff”, and that’s what we’re trying to make sure doesn’t happen.
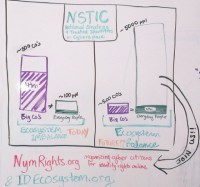
The problem with that (see left-hand image), on the left side there, that’s the current makeup of the NSTIC community: the tall purple thing you see is the big corporations that are involved in it, and it’s about 500 representatives there. And on the right, the little tiny green sliver is the regular people. And this could mean privacy groups like the EFF and Epic that could be like somebody like me: I have joined as aestetix as a member of NSTIC, which means anybody can do it, right? You don’t even have to be a US citizen, I’m serious; a lot of people just don’t realize this.
And what we’re trying to do with this outreach – see the one on the right? See how it’s like 5000 on the green side of all the ordinary regular people, and maybe still 500 corporations? It’s not that anything bad or malicious is happening; it’s just that we need to make sure that people’s voices are heard. So, think about this as we go through that these are really important discussions, if identity is important to you, then this might be something you’re interested in.
So, myth #1, and there are 5 of these myths, just so you know. Only pedophiles, criminals and cyber-bullies do not want to use their legal names online. Also, what is a “nym”? And we’re joined by Adam Savage who’s going to help us debunk some of these myths.
Let’s take a look at what is a “nym”, and nyms vs. names, things like that. These are just some typical ID type things (see left-hand image), all these little documents, some of them are government, some of them are not. How many people here have three or more of these IDs?
The other interesting thing I want to point out is that – let’s say you have all five of these, your name on each of them can be different and valid at the same time. That tells you a bit about how these systems all work together or don’t work together.
An example that I have used – I have a legal first and last name and I had a boarding pass when I was flying from Europe to America, I think I was at a conference or something; and the flight screwed up the name, so there was no space and it was all one word, and I came into border patrol and they tried to scan it and that broke the system, it didn’t work, because it was looking for compartmentalization and it couldn’t stomach it. Yeah, server fail, so the guy had to sit there and manually type it, I kind of felt bad for him, but he was an asshole to me, so fuck him, right?
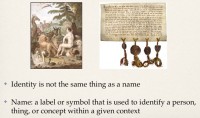
I started thinking more about what is a name and how does it relate to identity, and I think one important thing is that they’re not the same thing. I define here name as a label or symbol that is used to identify a person, thing or concept within a context.
Up on the left there you see Adam naming the animals, and if anybody studied Genesis at all, Adam names the animals and has a degree of power over them. And there’s also some discussion about the Adamic language, the language that was spoken inside of the Garden of Eden, and the true name of God and all this other stuff.
Later on in Genesis you have something even more interesting, which is the tower of Babel, where God comes along, or Yahweh I should say, the Old Testament God, destroys the language and makes everyone speak in a different tongue, thus destroying the tower of Babel. So, if you don’t think names have any power, take a look at Genesis.
And on the right there you have the royal seal that made sure it came from the king. So names can be used for authentication too, or symbolization I should say.
Here’s some various Nom de Plumes (see right-hand image). Nom de Plume is another form of the word for “pseudonym”, and we’ll get into etymology in a minute, but Nom de Plumes literally means “feather name”. I’m guessing in DC, how many people here know who Publius was? Besides the Roman century and whatnot, Publius was the name that was on all the Federalist Papers. There were three main authors of the Federalist Papers: it was James Madison, John Jay, and I always forget the third. Does anybody know? Hamilton, yes, thank you! They wrote letters to these newspapers to defend the constitution and make sure it will get ratified under the pseudonym of Publius.
J.K. Rowling, anyone heard of her? Do you know why it’s a pseudonym, by the way? Because her name is Joanne Rowling, she doesn’t have a middle name, and the publisher didn’t want to publish a book by a woman, and made her come up with a gender-neutral name. She added the K, the K is just made up for the book.
Nicholas Bourbaki is an interesting one; it was a group of, I think, French mathematicians in the 1930s who would try to write mathematics from the ground up. And one of my favorites here – Ian Donald Calvin Euclid Zappa – anybody know this story? They say your parents name you, right? So, Frank Zappa, anyone heard of Frank Zappa? He named his kids like Dweezil and Moon Unit, right?
So, Frank Zappa was in a hospital, and they gave birth to Dweezil, and the nurse is like: “Ok, what name do you want to give your kid?” And they’re like: “Dweezil”, and the nurse is like: “No, use a real name”. So, what Frank did is he just sat there and he listed off four random names of musicians he knew, and the nurse put that down on the birth certificate. So, move along five year later, and they’ve been calling him Dweezil all along, and the kid turns five and he discovers that the name on his birth certificate is that, and he’s like: “Fuck no, my name is Dweezil”. And he had his name at 5 years old legally changed to Dweezil.
Some other points here: Richard Bachman aka Stephen King; you have Deep Throat who is purported to be Mark Felt – that was all about the whole Watergate. He admitted it, ok. Voltaire who published Candide and the King of France wanted to kill the author of it but couldn’t. George Eliot, anyone know that? George Eliot’s actual name is Mary Anne Evans; it was a woman who couldn’t get published as a man, just like the Bronte sisters, who published under male pseudonyms because they couldn’t get published as women. That’s really interesting, isn’t it? Turns out there is an entire Wikipedia section on female writers who wrote under male or gender-neutral pseudonyms. That’s kind of fucked up, isn’t it?
So let’s move on a little bit and ask some questions about why names matter. There’s Valerie Plame, the CIA employee who was outed. Also you have things like the witness protection program, and most people will consider that a valid pseudonym being a cover shield.
Anybody remember the Odysseus and the Cyclops story, where he tries to escape the Cyclops’ cave, and Cyclops says: “Who are you?” And he says: “My name is no one?” So then he stabs the Cyclops in the eye and he escapes and Cyclops says: “Come help me, something horrible has happened” – “Well, who did this to you?” – “No one”. And they’re like: “What the hell?” This is a very old thing.
And then things like the AOL and Netflix databases, which they tried to anonymize the data they put out; this was a few years ago. And it turned out that people were able to take the search histories and collect them together and determine who the people were. So, interesting things to think about.
A couple of definitions here: a “social network” – I call that a force that brings people or their personas – it could be your IRC or any screen names or something like that – together on a regular basis. A “friend” is a person that you would choose to be in contact with. And really important in this discussion – an “institution” is a custom, practice, relationship, or significant behavior within a social network. And when I mean institution, I also think of phrases like “institutionalized depression”, and I’m sure people here are familiar with that term.
Moving on a little bit and getting into some psychology here, the question: “Is identity internal or external?” And if you’ve studied Freud at all, you may be familiar with the concepts of id, ego and superego, the id being the carnal beast nature of man, ego being the intellect, and superego – the relations between all of us. This gets in the questions of reputation – we’ll address this in a bit in the talk.
Has anyone here seen Citizen Kane, the movie? The thing that I really like about Citizen Kane is it’s a movie where the main character dies in the beginning, and the whole movie is trying to piece together who he is and what he was getting on about. And it’s kind of creating this integral of who he was based on other people’s perceptions of him, so gathering who he was based on external perception. So, interesting things to think about.
And then, of course, Oscar Wilde, who’s also a jackass and a misogynist, but really a funny snippy witty guy: “The only thing worse than being talked about is not being talked about.”
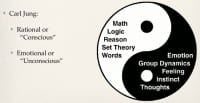
One of Freud’s students is Carl Jung, somebody who I’ve studied a great deal and I admire his work, defines identity in kind of two realms: you have the conscious and unconscious, or the rational and emotional. The rational is math, logic, set theory, things like that, and words – they’re all definitions, right? And on the unconscious, it’s emotion, group dynamics and feeling, and this is really important to think about when you’re thinking about names and thinking about defining words. The common language, right? That’s why common language is so important.
Jung has this other idea of collective unconscious as well, which is the mood of a room. How do you know when somebody’s upset? Just the general vibe. So these are really important ideas. To sort of revisit that for a second: you have a word, you have the definition of the word, and then you have the meaning of it, so the definition could be the word itself. Like “happy”: what does “happy” mean? Words are tricky things – you know, word salad, humans are really finicky beings.
So, I was thinking about this: how could this work within tech? And this is something I’ve been thinking about for a while. What I realized is that because we’re all online – we all use Twitter and Facebook; well, I don’t use Facebook, fuck them – but one of the things I realized is mentioned on the capstone there, it says: “Labels help define relationships.” (see left-hand image)
So, what you have there is what you just saw – the Jungian identity model. And then you have the relationship between Twitter, which I also consider a social group or a social network of sorts. And then that label, or the name that appears on it, is the way that we define or describe the relationship that I have with it.
Another one that you can see is the driver’s license, and the important element to remember here is that when we talk about personas, we talk about facets of somebody’s personality, and when we label them, it’s kind of like a prism, right? You have all the different colors that you label, and then you discover there’s more colors within them, and it’s very integral, right? I think identity works the same way, and names are simply labels for all these relationships we have with each other.
Something else I want to point out: you can see they’re labeled A, B, C and D, and D has a subset right there, where the driver’s license for John Smith is relationship C, because that’s the name describing that relationship with the government, the legal relationship. For D, your friends and family call you Jack, which, one could say, is derived from the legal name that you have, or the family name in some cases.
Does anybody know the origin of the word “nickname”, by the way? I think it’s Celtic; it literally means “additional name”, which means there’s a base name too, it means a name that’s extended away from the original one.
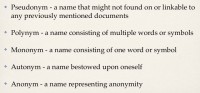
Back to what nyms are; we talked about names a lot, right? So, I’m defining a pseudonym – and by the way, when we say nyms, we usually mean that truncated nym part of the end of “pseudonym”, and that’s what most people think about. I believe it’s much more than that; we’re still having this vocabulary discussion within Nym Rights, so, this is my opinions.
I define a pseudonym as a name that is often used to hide a base name. And base name is very important – you have the original one and then hide it with a shield or something else. Witness protection program is an example of that.
A polynym is a name consisting of multiple words or symbols, so Charles Foster Kane or Dave Brown, something like that. A mononym is a name of just one word or symbol, so it could be Charles, it could be David, whatever. An autonym is something I really like, and you have to differentiate an autonym from a pseudonym, by the way. Autonym is a name bestowed upon oneself. Does anybody here have an autonym? A few people, ok, cool. And anonym is a name representing anonymity. And this is something I often refer to, if you’ve ever used Slashdot: when you make an account, you make a comment without logging in, you’re branded as an anonymous coward. So, just some basic definitions there.
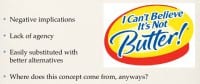
One of the core elements of this talk: why not use a real name? What’s wrong with that? Actually, first off, anybody, what’s the opposite of real? And you know what the etymology of pseudonym is, right? Pseudo is Greek for fake, or artificial and such. When we think of real and fake, we think of almost belonging and not belonging, and there’s kind of a negative implication with the word “real” or with things that are not considered real. Which is more valid? Which is more legitimate? Those are words I’ll get to in a bit.
There is also a lack of agency: how many of you chose what your name is? Ok, a few, so you didn’t even have a choice, what the fuck? And maybe you’re ok with that, but you should at least think about it. Easily substituted with better alternatives – I think given name, I think birth name, legal name – those are all totally fine. Those also represent and compartmentalize the ideas of names and something very different from real, and each of those is considered real. I’d say every name is real myself.
I could give an entire talk on where the concept of a real name comes from. The earliest origin that I found of it is English Common Law starting with Henry II – around the 1200s, somewhere in there I believe. Because they were running into this problem where all these little communities were trying to figure out property rights, they had to use Common Law to unite everything, and how are you going to tell who owns what? Well, then you need to have a name, right?
There are other examples where this comes in: the people who survived the plague, the Reformation of the Catholic Church, all these other elements, and of course the discovery of the New World. If you’re interested in that topic, it’s a brilliant topic. There was a talk given at the conference 28C3 called “What is in a name?” So, I recommend going to that, and we can talk later after that if you want.
Another thing that I want to go over is just what social networks are in general. Is anybody here familiar with Joseph Campbell? Has anyone here seen Star Wars? George Lucas credits Joseph Campbell in the Hero’s Journey with the creation of what Star Wars was about. And this is older than Campbell, by the way – the right hand path, the left hand path.
The right hand path is the institutionalization, the structure you were brought up in, the culture you come from. Maybe it’s the store down the street, the people that you knew, the way that you speak, the way you shake hands or bow, right? That’s all considered kind of the way things are supposed to be, the right hand path.
And the left hand path, which is also known as kind of the Hero’s Journey, is: when you go off into these realms of self-discovery. So you can see on the circle here, you have a guy, and there’s call to action, call to adventure – it could be when anyone gets a phone call, follows a white rabbit. And then you go a little bit longer, and you often get aids to work with – so, Luke gets the lightsaber. Then you go along, you have challenges, you get a mentor, maybe, so I think it was the Oracle or Obi-Wan Kenobi.
And you keep going until there is the abyss, and you get all these challenges as you run through them. And then you come to the atonement, which is bringing everything back together within itself, and then you return because you’re the same person, right? That’s something really interesting; I don’t have time to go through all of this, I could give an entire talk on just this.
I do want to focus on that question: “Why do hacker handles matter?” Anybody have an idea? Attribution is one thing; more within the context of the hero’s journey idea. What do you think? You are choosing your own identity, sure. One of the examples I’ve given to illustrate this point is… Everyone here knows what privileges are, I assume? I consider a name to be what I call an invisible privilege. If somebody has a long nose and you make fun of them, that’s a visible privilege; I consider a name an invisible privilege.
So, for example, how many of you have ever worn a tie to work? You know how everyone treats you differently when you have that tie on? It affects the mood; it affects the social network that you have. I run into this: if I introduce people by a name that they recognize as one of theirs. What if I introduce myself as Joseph Campbell and they didn’t know who it was? Well, I would get treated very differently than if I introduced myself as aestetix. And that’s something to just think about: “Why is it that we do that?” And this whole idea of what’s normal and where social norms come from, and that gets into Joseph Campbell’s ideas.
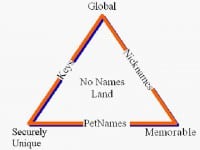
And one last thing on this myth I want to cover: do you guys know about the Zooko’s triangle? (See image) It comes from Zooko Wilcox-OHearn, he’s a cryptographer. The general idea here is that you have these three attributes for a digital name, a name, and a digital system. The name can be global, securely unique or memorable, and you can have two out of three, you can’t have all three, and that’s Zooko’s triangle paradigm.
If you want to understand this a bit better, there’s the analogous – fast, cheap and good, you can’t have all three, you can have two of the tree. An example that has been given for this is domain names, where you can have like abc.com, shmoocon.org – well, that’s global because everyone can access it from the URL, right? It’s memorable – everyone remembers that. It’s not really secure from, like, phishing attacks and things like that. And these are the caveats that we run into as we try to integrate all these contexts together, which is what the names are all about.
Number two for the myths, thanks Adam: “We can stop cyberbullying by forcing people to use their legal names. People who do not use their legal names do not contribute positively to discussions.” I had a freaking hour-long argument with the guy about this at NSTIC. Very nice guy, but we’re working on him.
Did anybody see this? (See left-hand image) This was the Violentacrez, the Reddit Gawker guy. He was creating this subreddit called “Jailbait”, where they were posting photos of underage women – fully clothed, just had that label “jailbait” on it. And there were also some boundaries issues and they were using the photos without permissions, and things like that. I’d be pretty pissed off if I was on there or if my daughter was on there, wouldn’t you, guys?
Here is the issue: I’m not saying the guy isn’t a douchebag; Violentacrez is the name, and his legal name is Michael Brutsch, this was all outed. I think it’s fantastic that there was some kind of justice brought to it, because it’s community standards and social things. The one issue that I really have with Adrian’s article is that it didn’t draw the distinction that it’s not because he used that name Violentacrez that he did these horrible things, it’s because he’s a douchebag that he did these horrible things.
The only time we see this in the news is when somebody is a freaking pedophile, child molester, criminal, things like that. Those are the only times these names ever pop up in the news, and for many people that’s the only exposure to them. There’s a lot of other folks who use them to have general common discourse – that’s why I used Publius in the example, right? Just disambiguate douchebaggery from names, very important distinction.
Next you have Amanda Todd (see right-hand image). Did any of you guys see this? This came up in the news the same week as that. This was absolutely horrible, very tragic story. This girl, she was 15 years old, she was cyberbullied and killed herself because of it. If you get a chance, go see this video; it’s about 8 minutes long and it covers horrible things that they did to her. But the challenge was: all of her cyberbullies were bullying her on Facebook, and if I recall, Facebook has a real names policy. And yet this kept coming up and people were saying: “We can’t use pseudonyms”. Wait a second, that doesn’t actually matter here. Cyberbullying is horrible and we definitely need to work on it, but it has nothing to do in this context with names.
I assume you guys know about Anonymous, or maybe you don’t? There’s a number of ways I’ve described Anonymous. In the examples here (see left-hand image) I used kind of the hive mind. You think of memetics – memetics are really important here because the only structure you have everyone following the top of the hierarchy, which is just an idea.
And over here does anybody recognize the photo on the left? Phineas Gage. Phineas was a railway worker; spike went through his brain in the 1850s, I think. And he stayed alive; he lived 10 years on after the accident. His personality changed though. And I think it’s really indicative of kind of the larger scope of how humanity works together – you have this notion of the hive mind, which is kind of what Anonymous is.
And how do people try to stop Anonymous? They try to take somebody out, tweak them a little bit, maybe put them through some Clockwork Orange therapy and reintroduce them into the system. Or: “Oh my god, there’s all these trolls, let’s try and step that out and force them to use their Facebook names,” something like that. Well, it turns out that it doesn’t actually work at all.
To address the first issue with it, it’s kind of like Heisenberg’s Uncertainty Principle or Schrödinger’s cat, because if you make a change in the system, you can no longer know how it operates.
And the second one – well, let’s ask TechCrunch (see right-hand image). A couple of years ago, I think it was March 2011, they decided to go for Facebook comments, and they did this to cut down on trolls. They were getting about 1000 comments per article a day.
A couple of days later (see left-hand image): “Facebook comments have silenced the trolls – but is it too quiet?” And they had a lot of issues, like why isn’t anybody commenting here anymore? They’re all using Facebook and it should be better, right?
And after a long deliberation, on January 22: “Commenters, we want you back.” (See right-hand image) They wound up going to the system called Livefyre which basically allows you to use Facebook; it also allows you to use Twitter and Google, or TechCrunch’s database and things like that. So they actually gave people a lot more choices, and it turned out, as you can see, 954 comments on that article, so they helped them get that better.
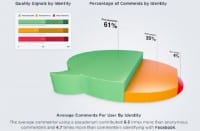
The thing that I want to point out here though is that if TechCrunch had researched this a little bit, they would have discovered that Disqus did a similar case study about a year before that (see right-hand image). And Disqus is similar; it’s kind of this plug-in thing where you can have users leave comments through it. And they have about 60 million users. It’s kind of hard to see on the slide, but the caps down here: “Pseudonyms are the most valuable contributors to communities because they contribute the highest quantity and quality of comments.” And they determined quality by whether it has been flagged for spam, whether it has been upvoted or replied to, things like that.
Here (see left-hand image) is a nice visual graphic: the green are pseudonyms, the red are “real” names, and the middle are anonymous users. So you can see 61% were pseudonyms, so that’s a lot of quantity, right? And that little bar graph up at the top, it’s kind of hard to see, but it’s segmented into three parts. On the left side you have positive, middle is neutral, and on the right is negative. So the interesting thing: on the top, the green part, 61% positive comments from pseudonymous users, whereas on the bottom, the red one was the real names – 51%. So they actually found that not only did they get more comments, but they had more quality comments from it all. So, something to think about.
There’s another question that comes up: what if people just don’t use names at all? There’s actually a social network that launched in December of last year called Social Number, and what it does is it allows you to log in and create an account picking a number, not a name. And as you can see here, people are leaving – this one is: “What do you do, or suggest can be done to handle some problem?” And the sender is not a name but it is a number.
And there’s a distinction I want to make here, because there’s a lot of confusion as to what pseudonomy and anonymity is. I don’t actually think this is anonymous; I believe that it is pseudonymous – people are choosing numbers because all the numbers are different, which means that it does not anonymize, it dehumanizes. And that’s a very important distinction.
Something else: I created a profile in here to see how it worked (see left-hand image). Check this out: this is the account settings profile, and notice they have Education here if you went to school, so they say “Education” in here, but not the name of your school. And then fast forward down a little bit – your work experience, how many years, maybe what your title is, the skills that you have, but not the place of your work. So it’s all the typical things that we find in a social network, all the names removed.
Here is an example of a post on there – ironically, about Anonymous (see right-hand image). Look at that – it’s a typical post, somebody’s blabbering on, and they have an avatar, a picture they’ve uploaded, and the name is simply a number. I mean, this just launched a couple of months ago, so it’s hard to say whether it will be successful, whether people will use it, how it will be used. But just something to consider – that there are efforts into this.
Myth #3: we cannot trust anyone who does not use their legal name online. Trust – that’s such a tricky word, isn’t it? Here’s a couple of examples: my friend ‘violet blue’, she is a sex-positive tech writer, among other things. She wound up having a fight, and she finally did get her name verified (see left-hand image below), because there was an impersonator, somebody else using the same name.
Twitter has this thing – that little triangle that you see there, the blue check mark, it’s verified identity. Have you guys seen this on Twitter before, by the way? It turns out that there are ways to fool people, and this Twitter account on the right here, that is a fake Twitter account created for Judge Denise Lind, who’s presiding over, I think, the Bradley Manning pre-trial.
And somebody actually created an account with her photo and her name and started posting all this stuff about how the Obama administration is forcing her to do all these bad things. There was a whole bunch of people who were overjoyed to see this. And they were like: “How do we know this is true?” And they started asking that, and that little image showed up on her profile, but it turned out that somebody actually edited the background of her Twitter page to add the verification in.
Here are some other examples you guys have probably seen before (see right-hand image). This is a CAPTCHA: how do I know that the person logging in is a human or not? This is basically a key signing log: if you have a GPG key or PGP, how do people trust you? Well, they sign your key, right? This is kind of a way that you can tell somebody’s trustworthy – in this case my late friend Lynne Sassman; how many people trust them. There’s some issues with that, but in general it’s at least one tool that we can try to use to get there.
Another one (left-hand image) you can see on the left here – SSL Certs, and on the right you have: what if somebody’s being a dick on Reddit, how do I know they’re not a sock puppet, how do I know they didn’t just create that account to log in and do something? Well, they’ve got a whole bunch of karma, so people have upvoted their comments and this stuff is verified. There are symbols that we can use to kind of verify, whatever the word “verify” means. It’s a way that we can establish trust within a community or social system, except when you try to turn it into a business.
Has anybody heard about Klout? Does anybody know how the fuck Klout works? Because I don’t, and all those people, including a wired.com article: one of the headlines is “Nobody gives a damn about your Klout score.” What the Klout score is it in theory goes through all these social networks and gives you a number between 0 and 100 based on how your Klout is, or your reputation, or your influence. But they don’t tell you how it works. Oh, 100 is Justin Bieber, ok. And they can game it for sale. Maybe they’ll be around, maybe they’ll be more transparent, but at the moment it’s kind of a joke to me.
If you see a question on here (see left-hand image) that sticks out to you, just come with me afterwards and ask me about it. Some of these questions have no answers, by the way; some of them are just rhetorical. Quick poll here: how many people here have a Facebook account? Ok, keep your hands up. How many of you have your job posted on Facebook? Ok, and of those: how many have your salary posted? So, what is transparency, right?
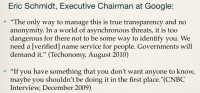
Myth #4: we can trust “identity providers” like Google and Facebook. Yeah, good one, Adam. So let’s look for a couple of quotes, just historically. Eric Schmidt, Executive Chairman at Google, you all may have heard of him; so the first quote here: “The only way to manage this (by this he means online identity) is true transparency and no anonymity.
In a world of asynchronous threats it’s too dangerous for there not to be some way to identify you. We need a verified name service for people. Governments will demand it.”
This is why I’m getting involved in NSTIC, and you guys should, too. The next one, check this out: “If you have something that you don’t want anyone to know, you shouldn’t be doing it in the first place.” Glad to see that he is the arbiter of morality. So, if you want this guy to dictate what you can do in the bedroom, there you go.
Now we have ‘King’ Zuckerberg, CEO at Facebook: “The days of you having a different image for your work friends or co-workers and for the other people you know are probably coming to an end pretty quickly. Having two identities for yourself is an example of a lack of integrity.” So, that’s Zuckerberg talking about integrity; that was before his sister got compromised.
My favorite, of course, is Chris Poole, founder of 4chan, there’s a success kid there: “Saw the school bully working in McDonalds.” Yeah! “The portrait of identity online if often painted in black and white. Who you are online is who you are offline.” “Identity doesn’t work that way, online or offline. It’s not who you share with, it’s who you share as;” and that’s one of the thesis points in my talk: “Identity is prismatic.”
Just to do a quick recap (see right-hand image) for the Google nym war stuff; and by the way, nym wars where all of our accounts got suspended, and a bunch of people fought back against Google, and that was called nym wars because people were fighting to keep the names that they had chosen on Google. It’s actually still unclear what their policies are, but we’ll get to that in a second.
The chronology: there was some confusion, and they requested my government issued ID, and I’m still not sure why or what they’re going to do with that. I never sent it to them, and please, anytime anybody asks for a government issued ID, ask them what law requires it, because if there’s a law requiring it, there’s probably a legal procedure for using it too.
That’s just something to think about. I started asking them some hard questions, and my account suddenly got reinstated. Then two weeks later I got suspended again.
I wasn’t alone (see right-hand image): ‘violet blue’, who we just saw in the Twitter thing – she was also suspended. There’s my friend Sai; he has a legal mononym, that’s his driver’s license, his full legal name is Sai.
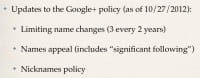
There’ve been some updates and changes to this policy of Google. The new policy: “You can change your name, but it’s limited to 3 times every two years,” I’m not sure why. “You can appeal (and one of the elements of the appeal, besides sending them the ID) if you can demonstrate that you have a significant following,” whatever that means.
They also have what’s called the Nicknames Policy, which I thought was interesting, because you may have heard that Google said that they were going to allow pseudonyms – some of you might have seen that. Well, this is what it looks like (see left-hand image). This is their idea of pseudonyms: you have your first name and last name, and then the nickname blank, and then it says: “Display name as.” And notice that the displayed name can either be your first or last name, first, nickname, last name, or first, last name and then your nickname.
When the entire point, to me, of using pseudonyms, or any kind of online ID, is to have the ability to separate contexts, this defeats the whole fucking point of that. So, just for you to think about.
By the way, Google cares about this so much, they’ve actually filed a patent for this as of September, 18 of last year (see right-hand image). You can see up there that there is the name, it’s like Sara Johnson, then the different nicknames, the personas you can have; at least they use the word “persona”.
You guys may have seen this if you tried to log into YouTube or something like that. This is where we’re going right now (left-hand image), and notice how it says: “Would you like to use your full name on YouTube?” or whatever service it is. And there’s the button down there that says: “I don’t want to use my full name.”
And look at this (see right-hand image). It comes up with this thing, it says: “Are you sure you don’t want to use your full name? Why not?” And you got these options: “My channel is for a show or a character,” “My channel is for a music artist or a group,” or “My channel is for personal use, but I cannot use my full name,” all these other things. Let’s see here, does this remind you guys of anything? There’s a lack of transparency, there’s procedures and policies that make absolutely no sense, and they seem to change around kind of sporadically.
Remind you guys of anything? (see left-hand image) TSA: “Opting out? Still let us know why,” – “It violates my constitutional rights,” “It violates my religious beliefs,” “I don’t want cancer,” my favorite, of course: “It simply does not fucking work.” I spent, like, an hour making that in Photoshop, because I thought it was funny. Apologies if it sucks.
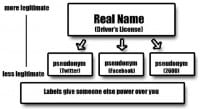
This is what I call Google’s method: we saw earlier in the talk the suggested method for online ID; this is the way Google is doing it (see right-hand image). You have the real name, which you saw in the patent; and then you have the hierarchy. Hierarchy is very important here, the top level and the lower level pseudonyms.
By the way, does anybody know the etymology of the word “legitimate”? Comes from “legitimare”, which is Latin for “to make lawful.” It shares roots with the words “law”, “legal”, “legislate”, things like that. So if you think about the context of it, if you call something legitimate, what is it that you’re really saying? It’s for legal use, of course. The capstone on this: labels give someone else power over you. I believe there’s a great deal of power involved in all of this.
By the way, Facebook is not innocent in this (see right-hand image). If you guys saw this, this was in September and it’s called “Snitchgate”. Basically, this pops up, and the text here says: “Please help us understand how people are using Facebook. Your response is anonymous,” blah-blah-blah. It says: “Is this your friend’s real name?” – “Yes, No, I don’t know this person,” blah-blah-blah. It’s asking people to snitch on their friends. Facebook took that down afterward; they claimed it was just a test thing. I’m like: what kind of institution is Facebook trying to create with this?
So, this just happened about two weeks ago (see left-hand image). Did anyone see this, the Instagram shit? Remember Instagram? It’s like the hipster photo website thing, where you download the app on your iPhone, it becomes a hipster and has vintage colors and things.
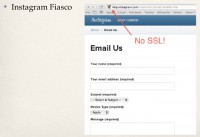
They got bought by Facebook for $1 billion, and just a couple of weeks ago they did this thing, where they were suspending users’ accounts under the terms of the Impersonation Policy. It actually says here: “In order to get their accounts back, they have to send in their government issued ID.”
One thing I want to share, by the way: this (see image above) is in the guidelines of Instagram’s Impersonation Accounts thing. It says they want two clear photographs of different angles on the government issued IDs, and there’s a nice little link there that says: “Submit the following information.” Ok, I’ll go ahead and click that and submit my ID – wait, there’s no SSL?! So, just insult and injury there (see left-hand image).
This is the state of things right now, this happened about two weeks ago, and if you want to keep using these services, this is why people need to speak up, basically, and say: “Here is what I think.” And if you disagree with me, that’s ok, because we want to have a public discourse about all of this.
Just a few more questions for a thought: who were Google and Facebook trying to “impress”? Who else might have access to this data? I have no fucking clue. And, of course, why would Chewbacca, an 8-foot-tall Wookie, want to live on Endor with a bunch of 2-foot-tall Ewoks? By the way, Chewbacca would have been suspended under Google’s Real Names Policy.
Our last myth from Adam here: we are currently fixing this through legislation. South Korea did this back in 2003 (see image below). So, South Korea, the Real Name Verification Law, this was passed in 2003 in response to some issues they were having around the election and people leaving snarky comments on web forums and such – Resident Registration Numbers, similar to a Social Security Number in a sense.
And they repealed this last year after the KCC, the Korea Communications Commission, discovered there was a 0.9% change in quality. They determined quality by basically curse words that were used. There were about 50 or 60 curse words, and also psychologists will appreciate this, they had this thing called anti-normative behavior. So, I guess going against the grain or something like that; it’s kind of unclear what it was.
If you want to learn more about that, Carnegie Mellon University did a follow-up study, and it’s very enlightening. But they repealed it because that’s 0.9%, and statistical significance is 5% or greater, and they didn’t even have that. So it turns out that pushing a certain type of name on people – maybe they’re douchebags to begin with, right, like the Violentacrez guy?
So, here is something that just happened on December 28, 2012 (see right-hand image). China passed this law “Strengthening Network Internet Protection.” You may have seen this in the news, where China basically passed this law requiring people to register their legal names in order to use the Internet.
And you can see here I bolded it: “Network service providers that handle website access services for users, handle fixed telephone, mobile telephone, and (I like this) other surfing formalities…” It’s really strange phrasing, maybe it’s lost in translation, because it was originally a Chinese law, but I’m not sure what a surfing formality is. And at the end there: “Require users to provide real identity information.”
So, what else is going on? Oh yeah, California, man; we’re just sucking right now. We had Prop 8, now we have Prop 35 (see left-hand image). Prop 8 was to ban gay marriage, by the way, and Prop 35: “Californians Against Sexual Exploitation”, and this was passed as of the last election.
Section 290.014(b): “If any person who is required to register pursuant to the Act (that is anybody who is a sex offender, basically) adds or changes his or her account with an Internet service provider or adds or changes an Internet identifier, is required to send that notification of this to law enforcement within 24 hours of said registration.”
Interesting, isn’t it? How easy is that to enforce? Anyone think that’s easy to enforce? The day after, on November 7, the EFF filed a lawsuit against that. An injunction was granted as of January 11, 2013.
It’s worth noting, by the way, that in the injunction grant one of the cases that was cited was the case McIntyre vs. Ohio Elections Commission from 1995. There’re basically 3 or 4 cases, or case law period in the US regarding anonymity. If you look in Wikipedia for Anonymous, they have this section on case law, and that’s, I think, the most recent – the others are from the 1940s and 1950s, or 50s and 60s or something.
The thing that I really like, I think it was Justice John Paul Stevens who said this, but one of the remarks in the 1995 case law: “Anonymity is a shield from the tyranny of the majority.” Look at Publius – that’s what our country is based on and founded on.
Germany has it right: they have this thing called the Telemedia Act. It was passed in 2007; section 13 (6): “The service provider must enable the use of telemedia and payment for them to occur anonymously or via a pseudonym.” So, Germany has actually codified into law that you must be able to use pseudonyms on the Internet. This has run into some issues of Facebook; they’re currently in a lawsuit with this right now, because the German government sued Facebook because of their real names policy. It’s going to be really interesting to see how this happens.
One of the issues we’re running into here is: corporations can set policies, right? But we also have law, and laws are agreed upon by the people, in theory, of represented democracy. What happens when what corporations want to do interferes with the written law of the land? At what point does that intersection meet? I think this is going to become a bigger and bigger issue as more things come online.
This is why all of you guys should get involved in NSTIC. Oh, it turns out Germany lost that case, interesting! So they said it is not a German law because Facebook is not sitting in Germany, so that was the day before yesterday? Ok, I was getting drunk at Shmoocon, I missed this. Wow, that’s fascinating, because there’s this juxtapose: we have a legal institution which people vote, you know. You can’t vote for Facebook, can you? Oh yeah, you can elect not to use it, which is why I don’t. They call it “liking.”
Basically, some final notes – I’m just about done and probably getting kicked off here soon. Nymrights.org is the URL, you can join the mailing list, we have a mailing list. Also anyone can join IDESG – Identity Ecosystem Steering Group, it’s kind of the group that’s formed around trying to enact the initiatives behind NSTIC. I’m registered as aestetix, so fuck that. They require a last name, and a period works as a last name, or a space sometimes. If you think about how that all goes – yeah.
So, if you’re worried about not wanting your legal name to be involved in something like this… I think I’m the first pseudonym actually to be an official member of NSTIC. In fact, I took this screenshot last night to just demonstrate it. It turned out there was somebody else – Snortly, I don’t know who that is. But yay – apparently they saw my Twitter pleas for it and they went ahead and registered with a mononym. So, we’re making a difference.
That’s it, any questions? 5 minutes, I’ll take questions.
So, somebody who is staying totally within the line, not doing anything wrong according to social standards and norms, is it necessary for them to have a pseudonym, is that what you’re asking? I think it depends on the context they’re in, in my opinion, people have the right to choose their own names.
That’s a fantastic question, I’m so glad you asked that. So let me repeat the question just to make sure I have it right: somebody like the Violentacrez guy, if their legal name is not known, how do we build an accountability? If somebody’s doing something illegal or amoral, depending on the social standards of morality, how do we find them?
Two answers to that; fantastic question. The first is that if you’re using the Internet, there’s a bunch of ways to find who you are: you could use it by IP address and access times. I can get more technical, but how many people here know how to find somebody if you don’t know their name? So it is possible, you’ve got a bunch of geeks around here who are happy to help enforce good.
On the other hand, and I’m going to cite William Binney, who is the NSA whistleblower, and in his talk – he gave a keynote at the Hackers on Planet Earth conference last year – he said that names are a really bad way to identify who somebody is. How many Dave Browns are there in the world? If you have like ten Dave Browns, how many of them are going to start using nicknames or pseudonyms and a unique identifier? There’s other ways, like habitual patterns, the schedule somebody keeps, where they work, things like that. There’s all kinds of ways you can identify somebody; an IP address is one of them.
4chan has actually run into issues with this. One of the things that Chris Poole has spoken out about is making sure that if somebody posts child pornography or something illegal on 4chan’s /b/ that they make sure that due process comes to them. Does that answer your question?
What am I really up to? Yes, Pinky, I’m trying to take over the world.