
 Computer security analyst Mikko H. Hypponen presents his talk at TEDxBrussels event dedicated to the present-day privacy concerns, providing specific examples of such breaches and emphasizing the consequences. Mr. Hypponen also speaks on the three groups of online attackers and outlines the differences in the objectives and tactics employed.
Computer security analyst Mikko H. Hypponen presents his talk at TEDxBrussels event dedicated to the present-day privacy concerns, providing specific examples of such breaches and emphasizing the consequences. Mr. Hypponen also speaks on the three groups of online attackers and outlines the differences in the objectives and tactics employed.
In the 1980s, in the communist Eastern Germany, if you owned a typewriter you had to register it with the Government. You had to register a sample sheet of text out of the typewriter, and this was done so the Government could track where text was coming from. If they found a paper which had wrong kind of thought, they could track down who created that thought.
We in the West couldn’t understand how anybody would do this, how much this would restrict freedom of speech. We would never do that in our own countries. But today, if you go and buy a color laser printer from any major laser printer manufacturer and print a page, that page will end up having slight yellow dots printed on every single page in a pattern which makes the page unique to you and to your printer. This is happening to us today, and nobody seems to be making a fuss about it. And this is an example on the ways that our own governments are using technology against us, the citizens. And this is one of the main three sources of online problems today.
If we look at what’s really happening in the online world, we can group the attacks based on the attackers. We have three main groups.
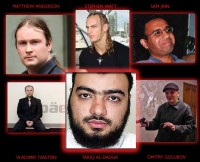
We have online criminals, like here we have Mr. Dmitry Golubov from the city of Kiev in Ukraine. And the motives of online criminals are very easy to understand: these guys make money. They use online attacks to make lots of money, and lots and lots of it. We actually have several cases of millionaires online, multimillionaires who made money with their attacks: Vladimir Tsastsin from Tartu in Estonia, Stephen Watt, Matthew Anderson, Tariq Al-Daour and others (see image). These guys make their fortunes online, but they make it through the illegal means of using things like banking trojans to steal money from our bank accounts while we do online banking; or with keyloggers to collect our credit card information while we are doing online shopping from an infected computer. The U.S. Secret Service two months ago froze the Swiss bank account of Mr. Sam Jain, and that bank account had 14.9 million USD on it when it was frozen. Mr. Jain himself is on the loose, nobody knows where he is.
And I claim it already today that it’s more likely for any of us to become a victim of a crime online than here in the real world. And it’s very obvious that this is only going to get worse. In the future, majority of crime will be happening online.

The second major group of attackers that we are watching today are not motivated by money. They are motivated by something else: motivated by protest, motivated by an opinion, motivated by the laughs. Groups like Anonymous have risen up over the last twelve months and have become a major player in the field of online attacks.
So those are the three main attackers: criminals who do it for the money, hacktivists like Anonymous doing it for the protest, but then the last group are nation states – governments doing the attacks. And there we look at cases what happened in ‘DigiNotar’; this is a prime example of what happens when governments attack against their own citizens. ‘DigiNotar’ is a certificate authority from the Netherlands, or actually, it was. It was run into bankruptcy last fall because they were hacked into. Somebody hacked it thoroughly. And I asked last week in a meeting with Dutch Government representatives, I asked one of the leaders of the team whether he found plausible that people died because of the ‘DigiNotar’ hack. And his answer was ‘Yes’. So how do people die as a result of a hack like this?
Well, ‘DigiNotar’ is a CA, they sell certificates. What do you do with certificates? Well, you’d need a certificate if you had a website that has HTTPS – SSL1 encrypted services, like Gmail. Now, we all or a big part of us uses Gmail or one of their competitors, but these services are especially popular in totalitarian states like Iran where dissidents use foreign services like Gmail because they know they are more trustworthy than the local services, and they are encrypted over SSL connection, so the local Government can’t snoop on their discussions. Except they can, if they hack into a foreign CA and issue rogue certificates – and this is exactly what happened with the case of ‘DigiNotar’.
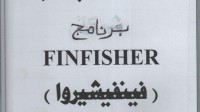 What about Arab Spring and things that have been happening for example in Egypt? Well, in Egypt the rioters looted the headquarters of the Egypt Secret Police in April 2011. And when they were looting the building, they found lots of papers. Among those papers – this binder titled ‘FINFISHER’ (see image). And within that binder were notes from a company based in Germany which had sold the Arab Egypt Government a set of tools for intercepting, and in very large scale, all the communication of the citizens of the country. They had sold this tool for 280,000 Euros to the Egypt Government. So Western governments are providing totalitarian governments with tools to do this against their own citizens.
What about Arab Spring and things that have been happening for example in Egypt? Well, in Egypt the rioters looted the headquarters of the Egypt Secret Police in April 2011. And when they were looting the building, they found lots of papers. Among those papers – this binder titled ‘FINFISHER’ (see image). And within that binder were notes from a company based in Germany which had sold the Arab Egypt Government a set of tools for intercepting, and in very large scale, all the communication of the citizens of the country. They had sold this tool for 280,000 Euros to the Egypt Government. So Western governments are providing totalitarian governments with tools to do this against their own citizens.
But Western governments are doing it themselves as well. For example, in Germany just a couple of weeks ago the so-called ‘Staatstrojan’ was found, which was a trojan used by German Government officials to investigate their own citizens. If you are a suspect in a criminal case, well it’s pretty obvious your phone will be tapped, but today it goes beyond that. They will tap your Internet connection, they will use tools like ‘Staatstrojan’ to infect your computer with a trojan, which enables them to watch all your communication, to listen to your online discussions, to collect your passwords.
And when we think deeper about things like this, the obvious response from people should be that “Ok, well… That sounds bad, but that doesn’t really affect me because I am a legal citizen. Why should I worry, ‘cause I have nothing to hide?”. And this is an argument which doesn’t make sense. Privacy is implied, privacy is not up for discussion. This is not a question between privacy against security; it’s a question of freedom against control. And while we might trust our governments right now and right here, any right we give away will be given away for good. And do we trust, do we blindly trust any future government, a Government we might have fifty years from now? And these are the questions that we have to worry about for the next fifty years. Thank you very much!
1 – SSL (Secure Sockets Layer) is a cryptographic protocol that provides communication security over the Internet.






























