This timeline fully reflects the state of the ransomware ecosystem over the period of May – December 2016. For your convenience, the entries are intuitively split up by the following categories: new ransomware released; existing ransomware updated; free decryptors created; and other important news on the e-extortion domain. The chronicle includes absolutely all ransomware events/incidents that occurred in the specified timeframe.
Read ransomware chronicle for 2017
Read ransomware chronicle for 2018
New ransomware released
Old ransomware updated
Ransomware decrypted
Other important ransomware related events
THE ENIGMA RANSOMWARE SURFACES
Targets Russian-speaking victims. Appends the .enigma extension. Creates the enigma_encr.txt ransom note.
CRYPTXXX 2.0 EDITION
Kaspersky’s free decryptor defeated. Concatenates the .crypt extension. Ransom notes named after victim ID.
SHUJIN RANSOMWARE SPREADING IN CHINA
Zeroes in on Chinese victims only. Very complex decryption routine. Uses the 文件解密帮助.txt ransom note.
GNL LOCKER (GERMAN NETHERLANDS LOCKER)
Targets German and Dutch users. Adds the .locked extension. UNLOCK_FILES_INSTRUCTIONS.txt manual.
CRYPTOHITMAN, A JIGSAW RANSOMWARE SPINOFF
Hitman video game themed. Appends the .porno extension and uses X-rated images on warning screen.
CRYPREN RANSOMWARE DISTRIBUTION UPTICK
Uses the .encrypted extension and drops READ_THIS_TO_DECRYPT.html help manual. Decryptable for free.
PETYA RANSOMWARE GOES WITH THE MISCHA BUNDLE
If the MBR-overwriting Petya fails to get admin privileges, it installs Mischa, a typical file-encrypting Trojan.
PETYA AND MISCHA COMBO AS PART OF A RAAS
Ransomware-as-a-Service platform launched allowing crooks to spread Petya and Mischa on an affiliate basis.
CRYPTXXX 2.0 CRACKED
Kaspersky Lab updated their free decryptor for CryptXXX ransomware, version 2.0 now covered.
8LOCK8 RANSOMWARE DISCOVERED
New sample. Adds the .8lock8 extension and creates READ_IT.txt ransom notes. Interaction over email.
SHADE RANSOMWARE UPDATE
New variant of the Shade aka Troldesh ransomware uses the .da_vinci_code extension to stain locked files.
FREE DECRYPTOR FOR GHOSTCRYPT AVAILABLE
GhostCrypt ransomware (.Z81928819 extension, READ_THIS_FILE.txt ransom note) decrypted by researchers.
SNSLOCKER HITS THE HEADLINES
New strain. Leverages AES cipher, appends the .RSNSlocked extension and demands $300 worth of Bitcoin.
XORIST RANSOMWARE LINEAGE DECRYPTED
Decryptor for the Xorist family released by Emsisoft. Requires one encrypted file and its original copy.
777 RANSOMWARE FAIL
Appends the ._[timestamp]_$[email]$.777 extension. Decrypted by Emsisoft’s Fabian Wosar.
NEW ZYKLON LOCKER IN ROTATION
A GNL Locker spinoff. Uses the .locked extension and drops UNLOCK_FILES_INSTRUCTIONS.html/txt manuals.
THE END OF TESLACRYPT: MASTER KEY RELEASED
TeslaCrypt ransomware authors close the project and release the Master Decryption Key.
WEBSITE-ENCRYPTING RANSOMWARE
New infection exploiting Drupal vulnerability. About 400 sites affected. Demands 1.4 BTC to decrypt content.
DMA LOCKER 4.0 DISCOVERED
Doesn’t modify filenames. Creates Cryptinfo.txt ransom manual and extorts 1.5 BTC.
CRYPTXXX UPDATED TO VERSION 3.0
Crypto flaw patched. Kaspersky’s decryptor no longer capable of restoring files.
TESLACRYPT DEVS RECOMMEND A RESEARCHER’S TOOL
Crooks provide a link to expert-tailored decoder on Tor payment site for the defunct TeslaCrypt.
ODCODC: NEW RANSOMWARE ON THE TABLE
File renaming format as follows: [attacker’s_email]-[original_filename].odcodc. Not decryptable for free.
ZCRYPT SPREADS VIA USB AND NETWORK SHARES
New one. Appends the .zcrypt string. Propagates over autorun.inf files on memory sticks and network drives.
ZYKLON RANSOMWARE SWITCHES TO APROPOS EXTENSION
New Zyklon edition switches from the .locked extension to .zyklon string. No more changes made.
BADBLOCK IS ON THE BLOCK
New BadBlock ransomware doesn’t append any extension to files. Ransom size is 2 BTC.
INVISIBLE EMPIRE THEMED TROJAN
Another Jigsaw ransomware version. Deletes files unless a victim pays up. Decryptable for free.
JOBCRYPTER UPDATE
A modified variant of the JobCrypter ransomware discovered. Uses the .css extension.
JUICYLEMON RANSOMWARE DISCOVERED
New sample telling victims to send email to support@juicylemon.biz for instructions. Demands 1000 Euros.
CRYPTXXX MORPHS INTO ULTRACRYPTER
Multiple design tweaks of ransom notes and payment page. Decryptor now called UltraDeCrypter.
GOOD NEWS: BADBLOCK DECRYPTED
The BadBlock strain, which cripples both data files and Windows EXEs, is decrypted courtesy of Emsisoft.
ANOTHER JIGSAW VARIANT EMERGES
This descendant of the Jigsaw ransomware displays NSFW wallpaper and uses the .paybtc extension.
BLACK SHADES CRYPTER WANTS A SMALL RANSOM
Targets English and Russian-speaking users, appends the .silent extension and demands $30.
HERBST RANSOMWARE TARGETING GERMAN USERS
This sample uses symmetric AES cryptosystem, appends the .herbst extension to files and extorts $50.
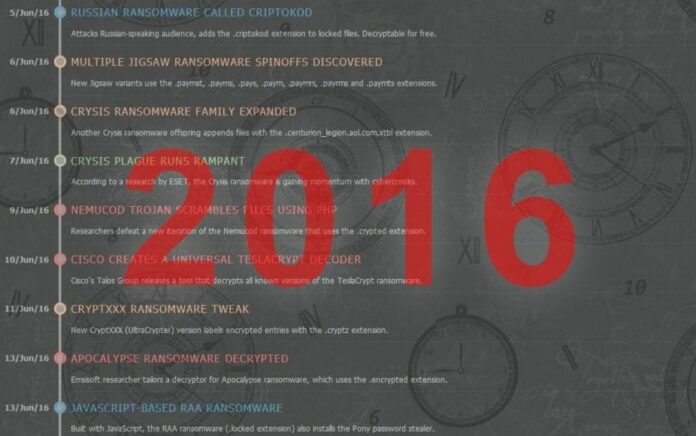
RUSSIAN RANSOMWARE CALLED CRIPTOKOD
Attacks Russian-speaking audience, adds the .criptokod extension to locked files. Decryptable for free.
MULTIPLE JIGSAW RANSOMWARE SPINOFFS DISCOVERED
New Jigsaw variants use the .paymst, .payms, .pays, .paym, .paymrs, .payrms and .paymts extensions.
CRYSIS RANSOMWARE FAMILY EXPANDED
Another Crysis ransomware offspring appends files with the .centurion_legion.aol.com.xtbl extension.
CRYSIS PLAGUE RUNS RAMPANT
According to a research by ESET, the Crysis ransomware is gaining momentum with cybercrooks.
NEMUCOD TROJAN SCRAMBLES FILES USING PHP
Researchers defeat a new iteration of the Nemucod ransomware that uses the .crypted extension.
CISCO CREATES A UNIVERSAL TESLACRYPT DECODER
Cisco’s Talos Group releases a tool that decrypts all known versions of the TeslaCrypt ransomware.
CRYPTXXX RANSOMWARE TWEAK
New CryptXXX (UltraCrypter) version labels encrypted entries with the .cryptz extension.
APOCALYPSE RANSOMWARE DECRYPTED
Emsisoft researcher tailors a decryptor for Apocalypse ransomware, which uses the .encrypted extension.
JAVASCRIPT-BASED RAA RANSOMWARE
Built with JavaScript, the RAA ransomware (.locked extension) also installs the Pony password stealer.
FLOCKER ATTACKS ANDROID GADGETS
The FLocker pest targets Android devices, including Smart TV, and extorts $200 worth of iTunes gift cards.
DED CRYPTOR BASED ON EDA2 PROOF-OF-CONCEPT
Affixes the .ded extension to files, imposes email interaction with the attacker and demands 2 BTC.
JIGSAW OFFSPRING PAYS HOMAGE TO THE ANONYMOUS
The Anonymous themed Jigsaw ransomware variant concatenates the .epic string to scrambled files.
DR.JIMBO@BK.RU RANSOMWARE SETS A DEADLINE
Instructs victims to reach the devs via email within 48 hours otherwise threatens to erase files.
CRYPT38 RANSOMWARE WITH WEAK CRYPTO
Targets Russian users, appends .crypt38 to files and asks for $15 in Rubles. Free decryptor released.
POTENTIALLY DECRYPTABLE CRYPTOSHOCKER
New sample using AES algorithm and appending the .locked extension. Experts found a workaround.
LOCKY DISTRIBUTION BACKED BY NECURS BOTNET
New Locky proliferation campaign discovered, leverages the Necurs botnet to generate harmful spam.
DECRYPTOR FOR APOCALYPSEVM RELEASED
Researchers create a decryptor for ApocalypseVM ransomware that uses advanced anti-VM features.
RUSSIAN USERS TARGETED BY KOZY.JOZY PEST
Uses asymmetric RSA crypto. Victims are instructed to email the attacker at kozy.jozy@yahoo.com.
CRYPTOROGER, A NEW SAMPLE OUT THERE
Employs AES algo, uses the .crptrgr extension and creates !Where_are_my_files!.html ransom note.
CRYPTXXX ADDS RANDOMNESS TO THE MIX
CryptXXX ransomware starts appending random 5-char extension to files instead of .crypz.
ZIMBRA RANSOMWARE ENCRYPTS EMAILS
Python-based strain. Targets the Zimbra open-source email platform. Ransom amounts to 3 BTC.
NEW APOCALYPSE SPINOFF DISCOVERED AND DECRYPTED
Appends the .SecureCrypted extension. Emsisoft Apocalypse Decryptor updated to restore files.
TOWERWEB@YANDEX.COM RANSOMWARE
Tells victims to email the dev at towerweb@yandex.com for instructions. Demands $100 worth of Bitcoin.
KRATOSCRYPT, A HIDDEN TEAR SPINOFF
Ransomware based on open-source educational code. Concatenates the .kratos extension to files.
BART RANSOMARE DOESN’T ACTUALLY UTILIZE CRYPTO
Stores files in password-protected ZIP folder rather than encrypt them. Demands 3 BTC.
SATANA BOOTKIT IS DOUBLE TROUBLE
Encrypts files and wreaks havoc with Master Boot Record. Displays a lock screen asking for 0.5 BTC.
THE DIDACTIC EDUCRYPT RANSOMWARE
Locks victims’ personal data but doesn’t request a ransom. Decrypt password available in a hidden .txt file.
ZEPTO EDITION OF LOCKY RANSOMWARE
New Locky variant appends the .zepto extension and renames files to 32 hexadecimal chars.
MONEY-HUNGRY MICROCOP INFECTION
Uses DES (Data Encryption Standard) and requests an astounding 48.48 BTC. Decrypted by analysts.
SHADE RANSOMWARE TWEAK
New Shade iteration switches from using the .da_vinci_code to .Windows10 extension.
AVG DEVISES DECRYPTORS FOR SIX RANSOMWARE STRAINS
The tools restore files scrambled by TeslaCrypt, Apocalypse, BadBlock, Crypt888, Legion, and SZFLocker.
UNLOCK92 RANSOMWARE
Targerts Russian-speaking audience. Email for interaction: unlock92@india.com. Decryptable for free.
EMERGENCE OF WILDFIRE LOCKER
A likely Zyklon copycat. Circulates mostly in the Netherlands and Belgium. Appends the .wflx extension.
ALFA RANSOMWARE DISCOVERED
Alfa, aka Alpha, ransomware uses the .bin extension and appears to be created by Cerber devs.
NEW APOCALYPSE VARIANT DECRYPTED
Emsisoft’s decryptor now handles the .bleepYourFiles version of the Apocalypse ransomware.
ANOTHER CRYPTXXX RANSOMWARE UPDATE
New edition creates README.html (.bmp, .txt) ransom notes and upsells a tool called “Microsoft Decryptor”.
THE BUGGY CRYPTOFINANCIAL SPECIMEN
Requests 0.2 BTC to unlock files but irreversibly deletes the data instead.
BITSTAK RANSOMWARE WITH WEAK CRYPTO
Appends the .bitstak extension to scrambled files. Researcher named Michael Gillespie created a decryptor.
PIZZACRYPTS PROPAGATING VIA NEUTRINO EXPLOIT KIT
Uses the .id-[unique_victim_id]-maestro@pizzacrypts.info extension to brand all encoded files.
THE PADCRYPT CAMPAIGN REVIVES
Having stayed dormant for several months, the PadCrypt ransomware (.padcrypt extension) re-emerges.
UNLOCK92 ENCRYPTION ENHANCEMENTS
New variant uses RSA-2048 cryptosystem, cannot be decrypted. Appends the .CCCRRRPPP extension.
A LAME CTB-LOCKER COPYCAT APPEARS
Sample dubbed CTB-Faker moves files to a password-protected ZIP archive. Potentially crackable.
ODCODC RANSOMWARE FINALLY DEFEATED
Researcher going by the handle BloodDolly came up with a method to decrypt ODCODC-encoded files.
NEW XORIST VERSION POSES AS CERBER
Although this sample uses the .cerber extension, it’s a mere copycat. Doesn’t link to Tor decryptor page.
WILDFIRE LOCKER ON THE RISE
According to OpenDNS, there is an upswing in WildFire Locker distribution via the Kelihos botnet.
LOW-COST STAMPADO RANSOMWARE FOR SALE
Appends the .locked extension. Criminals can buy a copy on the dark web for as little as $39.
DECRYPTION KEYS GIVEAWAY BY CRYPTXXX DEVS
For whatever reason, CryptXXX Tor payment sites provide free keys to decrypt .cryp1 and .crypz files.
PETYA RANSOMWARE UPDATED
Petya authors improved their Salsa20 algo implementation to encrypt Master File Table more reliably.
CRYPTXXX BADLY CRIPPLES FILENAMES
A fresh edition of CryptXXX replaces filenames with 32 hex characters and appends random extensions.
PYTHON-BASED HOLYCRYPT RANSOMWARE
Written in Python, the HolyCrypt sample installs all components as a single Windows executable.
AUTOMATIC ODCODC DECRYPTOR RELEASED
ODCODC ransomware victims can now use an automatic free decryptor. The infection’s C&C server is dead.
AVG CRACKS THE BART RANSOMWARE
Free recovery tool by AVG allows Bart ransomware victims to crack the ZIP archive password.
POWERWARE IS NOTHING BUT A LOCKY COPYCAT
PowerWare ransomware masquerades itself as Locky. Decryptor available courtesy of Michael Gillespie.
STAMPADO RANSOMWARE DECRYPTED
Emsisoft team member Fabian Wosar created a free decrypt tool for the relatively new Stampado pest.
CRYPMIC, A CRYPTXXX LOOKALIKE
CrypMIC bears a strong resemblance to CryptXXX. Researchers provide a comparative review of the two.
SIMPLE_ENCODER APPENDS FILENAMES WITH A TILDE
New sample. Uses the .~ file extension and creates _RECOVER_INSTRUCTIONS.ini ransom note.
THE NOMORERANSOM PROJECT GOES LIVE
A true breakthrough in fighting ransomware. Created by law enforcement agencies and security companies.
CHIMERA RANSOMWARE DECRYPTION KEYS RELEASED
Petya and Mischa ransomware authors publish about 3500 decryption keys for a strain called Chimera.
JANUS RAAS BECOMES OPEN TO WANNABE CRIMINALS
Crooks behind Petya and Mischa make their Ransomware-as-a-Service platform available to the public.
THE SHORT-LIVED JAGER RANSOMWARE
Incremental ransom size starting with $100 worth of Bitcoin. C&C server went down shortly after launch.
UYARI RANSOMWARE GOES AFTER TURKISH USERS
Appends the .locked extension to scrambled items. Ransom notes in Turkish asking for 2 BTC.
JIGSAW FAMILY KEEPS EXPANDING
“We Are Anonymous” Jigsaw ransomware variant with a new warning background. Decryptable.
KASPERSKY’S DECRYPT TOOL UPDATED
RakhniDecryptor solution by Kaspersky Lab decrypts Chimera-locked files with the keys previously leaked.
THE RAZY RANSOMWARE PREDICAMENT
New strain, uses AES crypto and concatenates the .razy extension. Even the devs cannot decrypt files.
LOCKY VARIANT USES BOOBY-TRAPPED WSF ATTACHMENTS
The Zepto version of Locky ransomware circulates via malware-tainted WSF email attachments.
SHINOLOCKER, A NEW PROOF-OF-CONCEPT
Japanese researcher creates educational ransomware called ShinoLocker. Another controversial initiative.
ASTONISHING SURVEY RESULTS
50% of U.S. companies were targeted by ransomware in the past 12 months, Osterman Research reveals.
CERBER RANSOMWARE 2.0 RELEASED
Switches to .cerber2 extension and uses a new desktop background. Ransom notes unaltered.
VENUS LOCKER, AN EDA2 SPINOFF
The EDA2 PoC gave birth to a new real-world strain. Uses AES-256 standard and appends .venusf extension.
HITLER-RANSOMWARE DISCOVERED
Buggy sample that deletes extensions rather than encrypt files. Demands a 25 Euros worth Vodafone card.
REKTLOCKER BASED ON EDUCATIONAL HIDDEN TEAR
Uses open-source Hidden Tear code with some modifications. Appends files with the .rekt extension.
RANSOMWARE ON IOT DEVICES
Researchers demonstrate a viable ransomware hitting thermostats at the DEFCON event.
SMRSS32 RANSOMWARE, A CRYPTOWALL COPYCAT
Impostor pretending to be CryptoWall. Installs manually via RDP. Appends the .encrypted extension to files.
PIZZACRYPTS AND JUICYLEMON DECRYPTED
Ransomware analyst nicknamed BloodDolly creates a free decryptor for PizzaCrypts and JuicyLemon strains.
POKEMONGO TROJAN DROPS ARABIC RANSOM NOTES
Appends the .locked extension. Creates a backdoor Windows user account (Hack3r) for future PC access.
TORRENTLOCKER TARGETS ITALIAN VICTIMS
Aka Crypt0L0cker. Uses the .enc file extension. Infects computers via rogue energy bills sent over email.
THE SHARK RANSOMWARE-AS-A-SERVICE
New RaaS platform that allows for extensive ransomware customization. Devs get 20% revenue cut.
CERBER RANSOMWARE DECRYPTION INITIATIVE
Check Point released a decrypt tool for .cerber and .cerber2 variants. Worked for only 1 day, though.
CERBER RAAS REVENUE UNCOVERED
According to an investigative research, Cerver devs’ annual revnue is on the order of $1 million.
NEW STRAIN TARGETING KOREAN VICTIMS
Based on the educational Hidden Tear code. Apparent ties to the CripMIC ransomware discovered.
APOCALYPSE RANSOMWARE AUTHORS GET UPSET
The crooks keep insulting Fabian Wosar who cracks every new edition of the pest.
CERBER DEVS PATCH FLAWS
Threat actors behind Cerber ransomware make Check Point’s automatic decryptor inefficient.
SMRSS32 RANSOMWARE DECRYPTED
Researchers release a free decrypt tool for the Smrss32.exe ransomware.
FSOCIETY RANSOMWARE DISCOVERED
An EDA2 spinoff. Sets a Mr. Robot TV series themed wallpaper with Fsociety hacking group logo.
BART RANSOMWARE SWITCHES TO REAL CRYPTO
Starts to actually encrypt files and append the .bart extension rather than simply password-protect them.
DETOXCRYPTO MIMICKING POKEMONGO FOR WINDOWS
Payload pretends to be PokemonGO game. Takes a screenshot of Windows screen for intimidation purpose.
ALMA LOCKER USES RANDOM 5-CHAR EXTENSION
Distributed via RIG exploit kit. Uses Tor C&C server. Ransom of 1 BTC to be submitted during 5 days.
ANOTHER CTB-LOCKER LOOKALIKE SURFACES
Another CTB-Locker copycat, uses a similar ransom note and color scheme. Demands 0.5 BTC.
THE PURGE MOVIE-THEMED GLOBE RANSOMWARE
Desktop wallpaper styling pays homage to the Purge movies. Appends the .purge extension to files.
WILDFIRE LOCKER TAKEDOWN
Dutch police and NHTCU agency seize WildFire Locker ransomware’s C&C server. Free decryptor released.
ALMA LOCKER DECRYPTION OPTIONS
According to PhishLabs, Alma Locker’s private key can be obtained with network sniffer during the attack.
FANTOM RANSOMWARE RUNS A FAKE WINDOWS UPDATE
New strain based on EDA2. Displays a bogus Windows update screen to obfuscate the encryption process.
DOMINO RANSOMWARE POSING AS KMSPICO
Based on educational Hidden Tear code. Payload disguised as KMSPico Windows crack.
LOCKY SWITCHES TO DLL INSTALLER TO AVADE AV
The Zepto alias of Locky ransomware begins leveraging a DLL installer rather than an executable to spread.
SMRSS32 RANSOMWARE USES U.S. ELECTION SPAM
New Smrss32 spam campaign delivering files masqueraded as U.S. Election news.
THE SERPICO VERSION OF DETOXCRYPTO
Targets uses in Serbia and Croatia. Doesn’t modify filenames. Requests 50 EUR for decryption.
FAIRWARE RANSOMWARE, A THREAT TO LINUX USERS
Adversaries compromise Linux servers, erase web folders and extort 2 BTC for recovery.
RAA RANSOMWARE APPEARS IN THE WILD
Instructs victims to send email to raaconsult@mail2tor.com for decryption steps.
THE CURIOUS CASE OF FABIANSOMWARE
Apocalypse ransomware devs name their new variant “Fabiansomware” to insult researcher Fabian Wosar.
CERBER SWITCHES TO USING A NEW EXTENSION
New edition of the Cerber ransomware concatenates the .cerber3 extension to locked files
REDIS SERVERS HACKED TO INSTALL RANSOMWARE
Crooks reportedly used insecure Redis servers to infect Linux machines with the Fairware ransomware.
STAMPADO STARTS SCRAMBLING FILENAMES
New Stampado variant replaces filenames with hexadecimal chars and uses the .locked extension.
THE NULLBYTE RANSOMWARE FAIL
Pretends to be a PokemonGO bot app. Demands 0.1 BTC. Decrypted by Michael Gillespie.
NEW CRYLOCKER IMPERSONATES A FAKE ORGANIZATION
Acts on behalf of inexistent Central Security Treatment Organization. Appends the .cry extension
CRYLOCKER DETAILS REVEALED
CryLocker propagates via Sundown exploit kit and sends victims’ details to its C2 server over UDP.
LOCKY SWITCHES TO AUTOPILOT MODE
New Locky samples go with built-in RSA keys and don’t communicate with C&C servers.
NO ACTUAL CRYPTO BY THE RARVAULT RANSOMWARE
Targets Russian users. Moves files to password-protected RAR archive, creates RarVault.htm ransom note.
KAWAIILOCKER GOES AFTER RUSSIAN-SPEAKING AUDIENCE
Hits Russian victims. Creates “How Decrypt Files.txt” ransom manual. Free decryptor released.
PHILADELPHIA RANSOMWARE SPOTTED IN THE WILD
New Stampado version sold on the darknet for $400. Features a Mercy button.
FLYPER RANSOMWARE POPS UP
Appends the .locked extension and requests 0.5 BTC. Attacker’s email address is flyper01@sigaint.org.
PYTHON-BASED CRYPY THREAT
Uses AES encryption, adds the .cry extension and drops README_FOR_DECRYPT.txt help file.
PHILADELPHIA RANSOMWARE DECRYPTED
Emsisoft’s Fabian Wosar creates a free decryptor for the Philadelphia pest.
CROOKS FORGE SUPPORT FOR THE HOMELESS
New Crysis ransomware rips users off under the guise of helping the homeless.
NOOBCRYPT TURNS OUT TO BE A LAME SAMPLE
New ransomware, uses the same set of crypto keys for all victims. Decryption keys published by analysts.
LOCKLOCK, ANOTHER EDA2 SPINOFF
Leverages AES-256 algo, appends the .locklock extension to files and creates READ_ME.txt ransom note.
NEW RAAS CALLED ATOM
Shark RaaS rebranded as the Atom Ransomware Affiliate Program. Available on the public Internet.
STAMPADO DECRYPTOR UPDATED
Fabian Wosar releases a decrypt tool handling new variants of the Stampado ransomware.
LOCKY PERSEVERES WITH OFFLINE ENCRYPTION
Locky ransomware’s autopilot crypto gets improved to prevent AV detection.
STAMPADO ENCRYPTS WHAT’S ALREADY ENCRYPTED
New version encrypts files that were locked by other ransomware strains, so it’s double trouble.
RAZY RANSOMWARE MIMICKS JIGSAW WARNING STYLE
Razy asks for 10 EUR worth PaySafeCard to unlock files. Ransom screen resembles one by Jigsaw ransomware.
FANTOM RANSOMWARE UPDATE
New edition can encrypt data offline, similarly to Locky. Now targets network shares.
FENIXLOCKER AUTHOR SPAWNS LOVE NOTES
FenixLocker ransomware dev found to leave the “FenixIloveyou!!” message in each encrypted file.
HDDCRYPTOR REWRITES MASTER BOOT RECORD
A highly dangerous sample that locks victims out of their computers by overwriting MBR.
FENIXLOCKER DECRYPTED
Emsisoft releases a free decrypt tool for FenixLocker, which adds secret mash notes to encrypted files.
FANTOM RANSOMWARE TWEAKS
New iteration sets desktop wallpapers randomly and derives ransom size from payload name.
STAMPADO AND APOCALYPSE UPDATED AND CRACKED
Fabian Wosar stays busy upsetting ransomware makers with his updated free decryptors.
LOCKY OPTS OUT OF OFFLINE-ONLY MODE
New Locky samples switch back to using C&C infrastructure for encryption, according to Avira.
CERBER CIRCULATION GROWTH
A major increase in Cerber ransomware distribution: daily infections reach 80,000.
CYBER SPLITTER VBS RANSOMWARE DISCOVERED
Spotted by GData, Cyber SpLiTTer Vbs asks for 1 BTC but fails to actually encrypt any files.
UNBLOCKUPC RANSOMWARE SURFACES
New sample, drops “Files encrypted.txt” ransom manual and demands 0.18 BTC for decryption.
MARSJOKE, ONE MORE CTB-LOCKER COPYCAT
Bears a strong resemblance to CTB-Locker. Mainly targets U.S. governmental and educational institutions.
NAGINI RANSOMWARE FOLLOWS POP CULTURE
Warning screen contains an image of Lord Voldemort, an evil character from the Harry Potter films.
NEW HELP_DCFILE RANSOMWARE
Named after ransom note help_dcfile.txt. Appends files with the .XXX extension.
THE DONALD TRUMP RANSOMWARE
In-development sample with a photo of Donald Trump on the ransomware GUI.
LOCKY GIVES BIRTH TO A NEW .ODIN PERSONA
New variant adds the .odin extension to files and creates _HOWDO_text.html/bmp ransom notes.
DXXD RANSOMWARE FINALLY CRACKED
Michael Gillespie, aka @demonslay335, creates a decryptor for the DXXD ransom Trojan.
OPEN-SOURCE RANSOMWARE FOR LINUX
New educational Linux ransomware called CryptoTrooper gets negative feedback from security community.
PRINCESS LOCKER WANTS TOO MUCH FOR DECRYPTION
Decryptor page resembles Cerber’s. The ransom is 3 BTC (about $2200), doubles after deadline.
AL-NAMROOD RANSOMWARE DECRYPTED
Appends the .unavailable extension. Emsisoft creates an automatic decrypt tool for this sample.
RAZY RANSOMWARE EXPANDS ITS GEOGRAPHY
New version targets German users. Extorts ransom in PaySafeCard. Deadline for payment is 72 hours.
KASPERSKY DISSECTS BRAZILIAN CYBERCRIME
A write-up by Kaspersky analyzes Brazilian TeamXRat ransomware that targets enterprises and hospitals.
NUKE RANSOMWARE SPOTTED
New one. Uses the AES standard and creates !!_RECOVERY_instructions _!!.html/txt ransom notes.
RANSOMWARE MAKER JOINS SECURITY FORUM
Apocalypse ransomware dev starts posting on BleepingComputer forums to insult researcher Fabian Wosar.
KASPERSKY DECRYPTS MARSJOKE RANSOMWARE
Kaspersky updated their RannohDecryptor solution to so that it can crack the MarsJoke ransomware.
TREND MICRO BEATS THE GLOBE RANSOMWARE
The Trend Micro Ransomware File Decryptor tool is now capable of decoding the Globe ransomware.
EMSISOFT CREATES THEIR OWN DECRYPTOR FOR GLOBE
The tool can crack the Blowfish cipher used by the Globe ransomware.
KILLERLOCKER USES A FRIGHTNING TACTIC
The strain appends files with the .rip extension and displays an image of a spooky clown.
FSOCIETY LOCKER BETA VERSION DISCOVERED
Concatenates the .realfsociety@sigaint.org.fsociety extension to files and drops fsociety.html ransom note.
CRYPTOLOCKER 5.1 BASED ON HIDDEN TEAR
Another example of criminals abusing educational ransomware code. No in-the-wild propagation.
MAJOR CERBER RANSOMWARE UPDATE
New variant adds a random 4-character extension and creates README.hta ransom note >>>
HADES LOCKER, A WILDFIRE LOCKER HEIR
Hades Locker occupies the niche of WildFire Locker, which had been taken down by Dutch law enforcement.
THE GLOBE RANSOMWARE FAMILY REPLENISHED
Globe devs release multiple new spinoffs appending the .encrypted, .raid10, and .globe extensions.
CZECH USERS ENDANGERED BY KOSTYA RANSOMWARE
Appends the .kostya extension. The ransom of 2,000 CZK (about $78) doubles after 12 hours.
THE COMRADE CIRCLE RANSOMWARE
Adds the .comrade extension to files and displays RESTORE-FILES![ID] ransom note.
ENIGMA RANSOMWARE UPDATE
New edition appends the .1txt extension and leaves enigma_info.txt ransom manual.
DEADLY FOR A GOOD PURPOSE RANSOMWARE
Uses AES-256 algo and requests a Bitcoin equivalent of $500. Configured to encrypt data in 2017.
VENISRANSOMWARE DISCOVERED
Uses VenisRansom@protonmail.com for communication. Enables RDP and steals passwords.
FIRST RANSOMWARE WRITTEN IN THE GO LANGUAGE
Detected as Trojan.Encoder.6491, it appends the .enc extension. Cracked by Doctor Web.
DXXD VERSION 2 DECRYPTED
Researchers create a decryptor for the 2nd iteration of the DXXD Ransomware.
NUKE RANSOMWARE UPDATE
New Nuke variant spotted in the wild. Concatenates the .nuclear55 extension to encoded files.
LOCKYDUMP TOOL RELEASED
Cisco Talos create LockyDump, a data aggregate with configuration parameters of all Locky versions.
EXOTIC RANSOMWARE ENCRYPTS EXECUTABLES
Dev’s handle is EvilTwin. Encrypts all data on target computers, including executable files.
NEW DMALOCKER VERSION DECRYPTED
Malwarebytes releases a tool that decrypts DMALocker’s latest !XPTLOCK5.0 version.
NOOBCRYPT RANSOMWARE TWEAK
NoobCrypt 2.0 demands $50. Attackers decided to stick with the ransomware name given by a researcher.
ANUBIS RANSOMWARE EMERGES
Based on EDA2 ransomware. Appends the .coded extension, attacker’s email is support.code@aol.com.
NEW SCREEN LOCKER SPOTTED
Only locks one’s screen without encrypting anything. Demands 10 EUR PaySafeCard to unlock.
7EV3N RANSOMWARE DECRYPTOR RELEASED
Malwarebytes researcher nicknamed “hasherezade” contrives a free 7ev3n Ransomware decryptor.
RANSOM TROJAN POSING AS A CLICK ME GAME
Obfuscates the encryption process with an amusing Click Me game.
JAPANLOCKER TARGETING WEBSITES
PHP-based ransomware encrypts data on web servers. Appears to have Indonesian origin.
MBRFILTER COUNTERS DISK-ENCRYPTING THREATS
MBRFilter tool by Cisco Talos blocks ransom Trojans that attempt to overwrite the Master Boot Record.
LOCK93 RANSOMWARE ASKS FOR RUSSIAN RUBLES
Low-quality sample. Appends the .lock93 extension to files and requests 1000 RUR. Decryptable.
ANGRY DUCK RANSOMWARE IS HUNGRY FOR BTC
Uses the .adk extension to brand affected files. Demands a huge ransom of 10 BTC.
N1N1N1 RANSOMWARE UPDATE
The variant uses a different filemarker (999999) and leaves the “decrypt explanations.html” ransom note.
LOCKY DEVS USE SOME BAD LANGUAGE
New version appends files with the .shit extension and creates _WHAT_is.html/bmp recovery manuals.
CHANGES IN THE BART RANSOMWARE
Now adds the .perl extension. Ransom notes are called recover.bmp and recover.txt.
THE THOR VARIANT OF LOCKY
Concatenates the .thor extension rather than the .shit string. Ransom notes unaltered.
A LOCKY COPYCAT WITH HUNGARIAN ROOTS
Dubbed “Hucky” (Hungarian Locky), the sample mimicks Locky’s wallpaper and ransom notes.
RANSOMWARE IMPOSING A SURVEY
An odd strain that asks victims to complete a sponsored survey before unlocking the computer.
CROOK TRIES TO SELL DECRYPT KEYS TO A RESEARCHER
Emsisoft’s Fabian Wosar declined “realfs0ciety” cyber gang’s offer to buy their decrypt keys on the cheap.
ANOTHER LAME SCREEN LOCKER
GData experts discover and defeat a screen locker that uses cuzimvirus@yahoo.com email for interaction.
ISSUES WITH THE CRYPTOWIRE PROOF-OF-CONCEPT
One more educational ransomware, CryptoWire, gave rise to a real-world sample.
ONYX RANSOMWARE TARGETS GEORGIAN USERS
Ransom message is written in Georgian. Warning screen contains an image of No-Face anime character.
THE OFFBEAT IFN643 RANSOMWARE
Leaves the IFN643_Malware_Readme ransom note. Requests $1000 worth of Bitcoin.
THE BUGGY JACK.POT RANSOMWARE
No mechanism to reach the attackers. Demands 3 BTC but provides a Litecoin address instead of Bitcoin.
MASTERBUSTER RANSOMWARE
Based on EDA2 open-source project. Drops ransom note called CreatesReadThisFileImportant.txt.
SCREEN LOCKER CALLED RANSOMWARE 2.0 SPOTTED
Does not encode any data but locks the screen instead. Demands 1 BTC otherwise threatens to delete files.
NEW SAMPLE USING !LOCKED#2.0 FILEMARKER
Discovered by Michael Gillespie, aka @demonslay335. Malwarebytes analysts create a decryptor.
ALCATRAZ LOCKER DISCOVERED
Appends the .alcatraz extension and leaves ransomed.html ransom note. Ransom size is 0.5 BTC.
CERBER NOW DISPLAYS VERSION NUMBER
Cerber Ransomware devs start indicating version number in v4.1.0 and onward.
SMASH RANSOMWARE ISN’T MUCH OF AN ISSUE
Displays a “File Kill Timer” window with a funny image of Super Mushroom. Doesn’t delete any files for real.
DUMMYLOCKER WITH HYBRID PROPERTIES
Encrypts data and locks a victim’s screen. Files are appended with the .dCrypt extension.
ZSCREENLOCKER VIRUS SUGGESTS BANNING ISLAM
Having encrypted one’s files, the zScreenLocker ransomware displays a “Ban Islam” image.
NEW ENCRYPTOJJS RANSOMWARE
Appends the .enc extension and creates “How to recover.enc.txt” ransom note.
PAYDOS RANSOMWARE, AN OLD SCHOOL STRAIN
Displays a ransom note within command prompt. Requests 0.33 BTC for the passcode to decrypt.
GREMIT RANSOMWARE EMERGING
New one. Concatenates the .rnsmwr extension to encoded files.
RSA PUBLISHES AN ARTICLE ON CERBER 4.1.x
Titled “The Evolution of Cerber… v4.1.x”, the article dissects new versions of the ransomware.
CLOCK.WIN32.RANSOMWARE SPOTTED
Doesn’t encrypt any data, simply displays a lock screen. Demands $20 through PayPal.
CERBER 4.1.4 APPEARS
Spreads via phishing emails with fake Word invoice attached. Version number indicated in ransom notes.
NOOBCRYPT RANSOMWARE UPDATE
New version uses an expired build of C# obfuscator. Accepts random, including blank, unlock key input.
CERBERTEAR, A CERBER COPYCAT
A variant of Hidden Tear proof-of-concept pretending to be the Cerber ransomware.
JIGSAW RANSOMWARE EDITION WITH FRENCH ROOTS
Decryptable sample that affixes the .encrypted extension to files and leaves a ransom note in French.
FSOCIETY RANSOMWARE APPENDING .DLL EXTENSION
Based on RemindMe ransomware. Uses .dll extension and drops DECRYPT_YOUR_FILES.html ransom note.
RANSOMWARE DISGUISED AS PAYSAFECARD GENERATOR
Uses a fake PaySafeCard generator window to obfuscate file encryption. Prepends “.cry_” to extensions.
AIRACROP RANSOMWARE BY TEAMXRAT RING
Appends the ._AiraCropEncrypted extension to files. Distributed by the TeamXRat cybercrime gang.
IRANSOM INFECTION KIT SOLD ONLINE
The sample can be purchased on underground resources. Adds the .Locked extension to data entries.
THE HEIMDALL PHP RANSOMWARE
A proof-of-concept written in PHP that targets web servers. Created by Brazilian researcher.
TELECRYPT RANSOMWARE DISCOVERED
The sample leverages the Telegram communication protocol to interact with its C2 infrastructure.
FAIRYTALE-ISH SAMPLE TARGETING RUSSIAN USERS
A new specimen using a popular Russian “Kolobok” fairytale theme for the desktop background.
FAKE OPM BANK NOTIFICATIONS SPREADING LOCKY
Spam emails disguised as alerts from U.S. Office of Personnel Management deliver Locky payloads.
CRYSIS RANSOMWARE DEVS RELEASE DECRYPT KEYS
CrySiS ransomware authors set up a Pastebin page with Master Decryption Keys for their infection.
KARMA RANSOMWARE MIMICKING PC OPTIMIZATION
New ransomware disguised as “Windows-TuneUp” app. Propagates over pay-per-install network.
PADCRYPT 3.0 AFFILIATE PLATFORM LAUNCHED
The updated PadCrypt version 3.0 can now be distributed on a Ransomware-as-a-Service basis.
THE ANGELA MERKEL RANSOMWARE
Displays a photo of Angela Merkel in the ransom notes. Asks for a BTC equivalent of 1200 EUR.
RANSOC SCREEN LOCKER’S PENALTY NOTICE
Locks the desktop rather than encrypt files. Blackmails users with sensitive content found on their PCs.
CRYPTOLUCK SPREADING VIA AN EXPLOIT KIT
CryptoLuck mimics the warning screen of CryptoLocker. Proliferates via RIG-E exploit kit.
RANSOMWARE TARGETING JPG FILES ONLY
Dubbed the “Demo” ransomware, this one only encodes JPGs and appends the .encrypted extension.
CROOK SEEKING RESEARCHER’S ASSISTANCE
One of Apocalypse ransomware devs contacts Emsisoft’s Fabian Wosar, asking for help with a code bug.
PCLOCK IN ROTATION AGAIN
A CryptoLocker copycat. Returns after almost 2 years of inactivity. Demands 1 Bitcoin for decryption.
PRINCESS LOCKER DECRYPTOR IN DEVELOPMENT
Researcher nicknamed ‘hasherezade’ gets close to cracking the Princess Locker ransomware.
GLOBE RANSOMWARE DECRYPTOR UPDATE
Fabian Wosar releases a decryptor for Globe2 (.zendr4, .raid10, .blt, .globe, and .encrypted extensions).
LOCKY ARRIVES WITH PHONY FLASH PLAYER UPDATE
A variant of the Locky ransomware found to be propagating via rogue Flash Player update sites.
.NET-BASED CRYPTON RANSOMWARE
Uses a mix of RSA and AES algorithms to lock files and demands 0.2-2 Bitcoins for decryption.
NEW SHELLLOCKER RANSOM TROJAN
One more sample coded with .NET programming language. Adds the .L0cked file extension.
THE DHARMA REINCARNATION OF CRYSIS
Dharma ransomware is a new variant of the defunct CrySiS. Uses the .[email_address].dharma extension.
THE HELPFUL “ID RANSOMWARE” PROJECT
The ID Ransomware service by MalwareHunterTeam now includes 238 ransomware strains.
CHIP RANSOMWARE SPREADING VIA RIG-E EK
New sample called the CHIP ransomware relies on the RIG-E exploit kit for proliferation.
NEW DEADLY RANSOMWARE VARIANT APPEARS
Corrupts victims’ data and provides no way to restore them due to a buggy key saving routine.
TRICKY OBFUSCATION BY PADCRYPT 3.0
Uses a rogue Visa Credit Card generator to camouflage payload execution.
LOCKY SPREADING VIA FACEBOOK SPAM
Malicious .svg images sent via Facebook’s instant messaging system install Nemucod Trojan and Locky.
CRYPT888 SETS A DEADLINE FOR PAYMENT
New variant claims to delete the AES-256 key unless a ransom is sent within 36 hours. Decrypted by Avast.
AESIR VERSION OF THE LOCKY RANSOMWARE
Appends the .aesir extension and leaves _[random_number]-INSTRUCTION.html/bmp ransom notes.
VINDOWS LOCKER IS NOT A MISSPELLING
New ransomware telling victims to call a “Microsoft Support technician”. Appends the .vindows extension.
PRINCESS LOCKER DECRYPTED
Security analyst @hasherezade defeats Princess Locker’s crypto and releases a decryption tool.
DECRYPTOR AVAILABLE FOR TELECRYPT
Malwarebytes releases a free decryptor for Telecrypt ransomware, which uses Telegram’s API.
MHT FILES DELIVERING LOCKY
Cisco Talos spot a Locky spam wave delivering booby-trapped MHT email attachments.
THANKSGIVING RANSOMWARE
New ransomware appears that displays an image of a turkey on its warning screen.
OZOZALOCKER IS NO BIG DEAL
Uses the .Locked extension and Santa_helper@protonmail.com email for communication. Decryptor available.
LOCKY’S NEW ZZZZZ VARIANT
Another edition of the Locky ransomware appending the .zzzzz extension to encrypted files.
CERBER RANSOMWARE 5.0 EMERGES
Proliferates via RIG-V exploit kit and spam. Still appends a random 4-character extension.
ONE MORE HIDDEN TEAR SPINOFF IN ROTATION
Based off of open-source Hidden Tear proof-of-concept. Uses a Jigsaw movie-themed background.
LOMIX RANSOMWARE USING CRYPTOWIRE’S CODE
A byproduct of educational ransomware project called CryptoWire. Asks for a Bitcoin equivalent of $500.
COCKBLOCKER AKA RANSOMWAREDISPLAY
Appears to be an in-development ransomware sample. Appends the .hannah extension to locked files.
CERBER’S RANSOM NOTE TWEAK
New variant of the Cerber ransomware creates _README_.hta ransom notes.
NEW SCREEN LOCKER BEING DISTRIBUTED
Claims to have found viruses and displays “Your computer is locked!” warning. Unlock password released.
CRYPTER RANSOMWARE TARGETING BRAZILIAN USERS
Attack are isolated to Brazil. Renames files rather than encrypt them. Demands 1 Bitcoin for recovery.
A PRIMITIVE SCREEN LOCKER DISCOVERED
Displays “Your Windows Has Been Banned” message. The unlock password is 123456.
THE UNUSUAL KANGAROO RANSOMWARE
An Apocalypse ransomware spinoff. Encrypts files and displays a warning screen before Windows boots up.
VINDOWS LOCKER DECRYPTED
Security researchers create a decryptor for Vindows Locker, which uses tech support scam tactic.
SAN FRANCISCO MUNI HIT BY RANSOMWARE
HDDCryptor ransomware paralyzes San Francisco Municipal Transit Agency’s IT infrastructure.
NEW RANSOMWARE BASED ON POWERSHELL
This PowerShell-based sample uses the ps2exe script and overwrites the original files.
HTCRYPTOR HARNESSING HIDDEN TEAR CODE
HTCryptor’s code is based on open-source Hidden Tear ransomware. Tries to disable Windows firewall.
SFMTA DENIES DATA THEFT
San Francisco Muni’s officials deny allegations about corporate data being stolen by ransomware devs.
NMOREIRA RANSOMWARE CRACKED
Emsisoft analyst Fabian Wosar creates a free decryptor for NMoreira/XPan ransomware.
RANSOMWARE ATTACKS A CANADIAN UNIVERSITY
Unidentified rasomware sample compromises Carleton University in Canada, demanding 39 BTC.
JIGSAW RANSOMWARE’S NEW CAMOUFLAGE
A new Jigsaw variant uses a phony Electrum Coin Adder app’s GUI to mask the ransomware installation.
ZETA RANSOMWARE STAINING FILES WITH NEW EXTENSION
New edition of the Zeta ransomware uses .rmd extension and # HELP_DECRYPT_YOUR_FILES #.txt ransom note.
TORRENTLOCKER UPDATE
The latest version of TorrentLocker, aka Crypt0L0cker, appends files with 6 random characters.
PRINCESS LOCKER CHANGES TAKING EFFECT
New iteration uses random extensions of 4-6 chars and !_HOW_TO_RESTORE_[random].txt ransom note.
MATRIX RANSOMWARE USING GNUPG
This sample locks data using the free GnuPG implementation of OpenPGP cryptographic standard.
MORE FREE DECRYPTORS BY AVAST
Avast releases 4 free decrypt tools for CrySiS, Globe, NoobCrypt and Alcatraz Locker ransomware strains.
ALPHA LOCKER FOR SALE ON DARKNET RESOURCES
Wannabe crooks can purchase the new C# based Alpha Locker ransomware on underground forums for $65.
HIDDEN MESSAGE IN NMOREIRA/XPAN CODE
Code of the updated ransomware contains a message to Fabian Wosar who cracked the previous version.
THE IN-DEV PHOENIX RANSOMWARE
Based on the Hidden Tear POC. Appends the .R.i.P extension to files and drops Important!.txt ransom note.
PADCRYPT 3.1.2 GOES LIVE
Version 3.1.2 of the PadCrypt ransomware is out. This build doesn’t feature any noteworthy changes.
RANSOMWARE DEV ARRESTED IN RUSSIA
The man nicknamed “Pornopoker” is accused of creating and distributing Ransomlock.P police ransomware.
NEWEST NEMUCOD VARIANT CRACKED
Emsisoft’s Fabian Wosar creates a decrypt tool for the latest variant of the Nemucod ransomware.
NEW ITERATION OF THE APOCALYPSE RANSOMWARE
The updated Apocalypse Trojan leaves *md5*.txt ransom note and a new extension with country code in it.
ANOTHER GLOBE RANSOMWARE VERSION IS OUT
New sample. Adds the .8lock8 extension and creates READ_IT.txt ransom notes. Interaction over email.
SHADE/TROLDESH RANSOMWARE DISTRIBUTION TWEAK
New Shade, aka Troldesh, ransomware variant (.no_more_ransom extension) uses the Kelihos botnet to spread.
NEW SCREEN LOCKER THAT DOESN’T FUNCTION RIGHT
It’s supposed to lock one’s screen and encode files (.encrypted extension), but the crypto part doesn’t work.
LOCKY STARTS USING THE .OSIRIS EXTENSION
New Locky ransomware variant appends the .osiris extension and drops OSIRIS-[4_chars].htm ransom notes.
GOLDENEYE RANSOMWARE, A PETYA HEIR
Affects master boot record (MBR) and encrypts master file table (MFT), thus completely blocking PCs.
NASTY MARKETING OF POPCORN TIME RANSOMWARE
Victims are suggested to infect two more users and thereby get their decryption key free of charge.
JIGSAW VARIANT CALLED THE “HACKED” RANSOMWARE
New Jigsaw ransomware build featuring “HACKED” logo. The ransom size starts at 0.25 BTC.
NEW SAMSAM RANSOMWARE SPOTTED
Appends the .VforVendetta file extension and leaves 000-PLEASE-READ-WE-HELP.html ransom note.
EDA2/HIDDEN TEAR VARIANT FOR SALE
A cybercrime ring made tweaks to open-source EDA2/Hidden Tear code, now selling it on the dark web.
CRYPTOWIRE POC GIVES BIRTH TO REAL THREATS
Crooks use new proof-of-concept ransomware called CryptoWire to create Lomix and Ultralocker strains.
ULTRALOCKER, A CRYPTOWIRE SPINOFF
Arrives at PCs with malicious Microsoft Wod documents. Demands a BTC equivalent of $1000 for decryption.
CYBER SPLITTER 2.0 DISCOVERED
Cyber SpLiTTer Vbs ransomware version 2.0 is out. Based off of the Hidden Tear POC. Demands 0.5 BTC.
THE LOCKED-IN RANSOMWARE APPEARS
Ransom notes are called RESTORE_CORUPTED_FILES.html. The payment deadline is set to 15 days.
CHIP RANSOMWARE UPDATE
Now uses the .dale extension and leaves DALE_FILES.txt ransom note.
DEADLY_60 SCREEN LOCKER SPOTTED
Uses an animated Matrix-style lock screen. Demands a Bitcoin equivalent of $400.
PADCRYPT UPDATED TO VERSION 3.1.5
Other than the new version number, no significant differences from the previous edition.
M4N1F3STO VIRUS WITH LOW IMPACT
Locks the screen and asks for 0.3 BTC. The unlock code is “suckmydicknigga”.
SAMAS RANSOMWARE GROUP EARNINGS REVEALED
According to Palo Alto Networks, the Samas ring’s profits in 2016 amounted to more than $450,000.
THE PORTUGUESE PAYDAY RANSOMWARE
A Hidden Tear spinoff. Uses the .sexy extension and drops !!!!!ATENÇÃO!!!!!.html ransom notes in Portuguese.
“YOU HAVE BEEN HACKED!!!” RANSOMWARE
Appends the .Locked extension to encrypted files and demands 0.25 BTC. Steals passwords along the way.
NEW KRAKEN RANSOMWARE
Renames files to base64 strings, adds the .kraken extension and creates _HELP_YOUR_FILES.html ransom notes.
“YOUR WINDOWS HAS BEEN BANNED” SCREEN LOCKER
Claims to have banned a victim’s PC for terms of use violations. The unlock code is “nvidiagpuareshit”.
CRYPTOMIX RANSOMWARE UPDATE
Uses the .lesli extension. Ransom notes are called INSTRUCTION RESTORE FILE.txt.
LOCKED-IN RANSOMWARE DECRYPTED
Michael Gillespie (@demonslay335) releases a free decryptor for the Locked-In ransomware.
NEW CERBER DISTRIBUTION TACTIC
Cerber ransomware payload arrives with rogue credit card reports that dupe users into opening a Word attachment.
ANOTHER XORIST VARIANT DISCOVERED
New edition of the Xorist ransomware appends the .antihacker2017 string to files. Decryptable for free.
GLOBE RANSOMWARE UPDATE
The only tweak is the new unlockvt@india.com extension for mutilated files. Demands 1.5 Bitcoin.
CIA SPECIAL AGENT 767 TROJAN
Clone of the M4N1F3STO screen locker using a new background. The unlock code is the same (see above).
NEW FENIXLOCKER VARIANT RELEASED
Drops “Help to decrypt.txt” ransom manual and provides thedon78@mail.com email address for payment directions.
KOOLOVA RANSOMWARE TARGETS ITALIAN USERS
This sample is currently in development. Only scrambles data in the Test path on a targeted computer’s desktop.
“NO MORE RANSOM” PROJECT ENGAGES NEW PARTNERS
Bitdefender, Emsisoft, Trend Micro and Check Point are now on the team. 32 new decryptors added, too.
AD-SUPPORTED BANDACHOR TROJAN DISTRIBUTION
New BandaChor ransomware spreads via malvertising on X-rated sites and an e-commerce web page.
CHRIS’ EXPERIMENTS OVER HIDDEN TEAR
Researchers spotted an instance of tweaking the Hidden Tear code by a wannabe crook named Chris.
THE BUGGY CRYPTORIUM RANSOMWARE
New sample using the .ENC extension. Simply renames files rather than encode them.
A GLOBE RANSOMWARE REPLICA
Analysts discovered a Globe clone that appends the .crypt extension and leaves HOW_OPEN_FILES.hta note.
CERBER RANSOMWARE’S IP RANGE CHANGED
According to MalwareHunterTeam, Cerber starts using several new IP ranges for UDP statistics.
GLOBE RANSOMWARE TWEAK
The updated infection switches to using the rescuers@india.com email address for interaction with victims.
DHARMA RANSOMWARE UPDATE
New Dharma edition instructs victims to reach the attacker via amagnus@india.com email address.
CRYPTOBLOCK RANSOMWARE IN DEVELOPMENT
Researchers discover CryptoBlock strain whose ransom notes resemble Cerber’s. No actual encryption yet.
ANDROID BANKING TROJANS EVOLVE
New variants of Android banking malware turn out to accommodate ransomware properties.
RANSOMFREE TOOL COMBATS RANSOMWARE
The RansomFree app by Cybereason detects and blocks over 40 widespread ransom Trojans.
APOCALYPSE RANSOMWARE TWEAK
Creates *MD5*.txt ransom note and uses cryptcorp@inbox.ru for interacting with victims.
M4N1F3STO SCREEN LOCKER STARTS USING CRYPTO
New edition of M4N1F3STO screen locker encrypts data along the way. Decryption routine is buggy.
MNS CRYPTOLOCKER SURFACES
Leaves RESTORE_YOUR_FILES.txt ransom manual and uses alex.vas@dr.com email address for communication.
KASPERSKY’S RANNOHDECRYPTOR TOOL UPDATED
RannohDecryptor now handles CryptXXX ransomware variants using the .crypt, .crypz and .cryp1 extensions.
NEW VARIANT OF SAMAS RANSOMWARE GOES LIVE
Appends .theworldisyours extension and creates CHECK-IT-HELP-FILES.html ransom note.
NEW GO-BASED RANSOMWARE SAMPLE
Written in Go, the strain uses .braincrypt extension and !!! HOW TO DECRYPT FILES !!!.txt ransom manual.
ENKRIPSIPC RANSOMWARE SPOTTED IN THE WILD
Aka IDRANSOMv3, targets Indonesian users. Decrypted by Michael Gillespie (@demonslay335).
MANIFESTUS RANSOMWARE APPEARS
Mimics a Windows update while encrypting data. Demands 0.2 BTC for decryption.
PROPOSALCRYPT IS UNDERWAY
New sample. Appends the .crypted extension to files and asks for 1 BTC. Decrypted by Michael Gillespie.
PADLOCK SCREENLOCKER IS EASY TO GET AROUND
Researchers found a way to defeat the PadLock screen locker. The unlock code is ajVr/G\RJzoR
FREE-FREEDOM RANSOMWARE MADE BY A TEENAGER
The alert by Free-freedom ransomware says it was coded by a 13-year-old boy. The unlock code is ‘adam’.
BLEEPINGCOMPUTER RELEASES A USEFUL TUTORIAL
Researchers at BleepingComputer publish a comprehensive guide on ransomware protection.
CERBER RANSOMWARE CHANGES ITS TACTIC
New Cerber edition doesn’t delete Volume Shadow Copies and primarily targets Microsoft Office documents
WINNIX CRYPTOR TEAM CAMPAIGN DISSECTED
The Winnix Cryptor Team ransomware is executed on servers via a BAT file and uses GPG crypto.
CERBER OPTS FOR NEW IP RANGES FOR STATS
Cerber starts using 115.22.15.0/27, 114.23.16.0/27, and 91.239.24.0/23 IP ranges for UDP statistics.
THE OBNOXIOUS GUSTER RANSOMWARE
New sample. Alerts victims with an irritating warning screen and audio. Appends the .locked extension.
FREE-FREEDOM MORPHS INTO ROGA RANSOMWARE
Coded by the already familiar Adam kid. Appends the .madebyadam extension. Decrypt password is ‘adamdude9’.
KOOLOVA RANSOMWARE WANTS TO TEACH YOU A LESSON
New in-dev version of Koolova decrypts files for free if a victim reads a few articles about ransomware.
ONE MORE CRYPTOLOCKER COPYCAT
Another sample calling itself CryptoLocker concatenates the .cryptolocker string to encrypted entries.
CERBER DEVS ARE IN HOLIDAY MOOD
The bad guys are getting ready to celebrate. Several C2 domains used by Cerber have ‘christmaas’ in their URLs.
VENUS LOCKER UPDATE
New variant of the Venus Locker ransomware demands 1 BTC and sets a deadline of 72 hours.
ALPHABET RANSOMWARE IS ON ITS WAY
The sample is still a debug version, hence not fully functional. Provides the decrypt key for free at this point.
GLOBEIMPOSTER RANSOMWARE DEFEATED
A Globe ransomware copycat using the .crypt extension and HOW_OPEN_FILES.hta ransom notes. Decrypted by Emsisoft.
DERIALOCK SCREEN LOCKER DISCOVERED
Demands $30. Victims must contact “Arizonacode” Skype user for payment steps. The code contains an “unlock all” command.
CERBER RANSOMWARE TWEAK
The update has brought about new IP ranges for statistical purposes, as well as _[random]_README.hta/jpg ransom notes.
BADENCRIPT RANSOMWARE APPEARS
Appends the .bript extension to mutilated files and leaves a recovery walkthrough called More.html.
NEW JIGSAW RANSOMWARE VERSION RELEASED
The new .hush extension being added to files is the only change made to Jigsaw in the course of this update.
NMOREIRA RANSOMWARE DECRYPTOR UPDATED
Emsisoft’s Fabian Wosar makes changes to his NMoreira decryptor, which can now handle the .maktub extension variant.
ODCODC RANSOMWARE RE-EMERGES
Creates HOW_TO_RESTORE_FILES.txt ransom note and uses the C-email-[attacker_email_address]-[filename].odcodc extension.
LG SMART TV TARGETED BY A SCREEN LOCKER
Android ransomware attacks LG Smart TVs, generating an FBI-themed lock screen and asking for $500 to unlock.
ANOTHER COMMONPLACE SAMPLE GOES LIVE
A new strain spotted that appends the -opentoyou@india.com extension to files and drops !!!.txt ransom note.
KILLDISK MALWARE GETS NASTIER
The file-deleting virus called KillDisk can now encode data. The ransom amounts to hundreds of Bitcoins.
ROGUE ANTIVIRUS INSTALLER SPREADS RANSOMWARE
A sample of the GoldenEye ransomware was found to proliferate via a bogus ESET AV installer.
DHARMA RANSOMWARE GOES WITH NEW RANSOM NOTES
The mkgoro@india.com version of the Dharma ransomware uses HTA format for its ransom notes (Info.hta)>>>
SAMAS INFECTION UNDERGOES A CHANGE
New Samas ransomware iteration uses the .whereisyourfiles extension and WHERE-YOUR-FILES.html help file.
PROOF-OF-CONCEPT RANSOMWARE CRITICIZED
An article posted on MalwareTech blog explains why open source ransomware is a bad idea.
EDGELOCKER, NEW RANSOMWARE ON THE TABLE
Concatenates the .edgel extension to mutilated files. The ransom amounts to 0.1 BTC.
New ransomware released
Old ransomware updated
Ransomware decrypted
Other important ransomware related events