
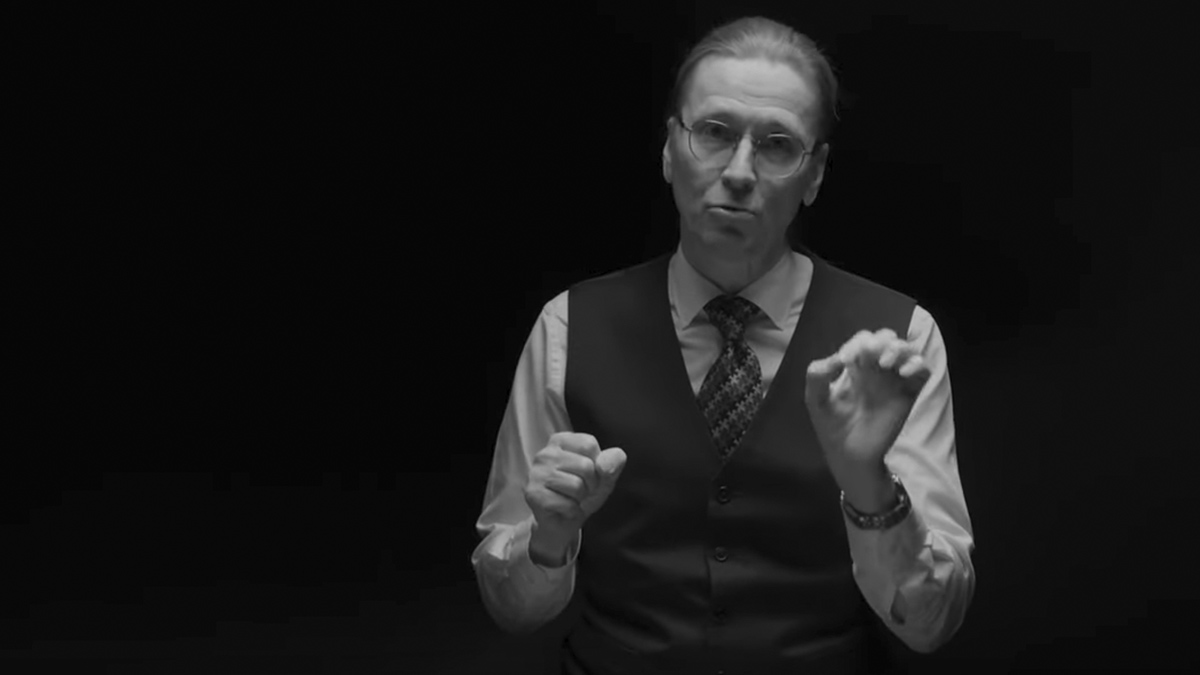
Finnish security expert Mikko Hypponen elaborates on what he dubs the “security tetris” paradigm, in which successes are invisible and failures accumulate.
Cybersecurity tetris
Whenever cybersecurity is in the headlines, it’s always bad news. Yet another company got hacked. Yet another data leak. Yet another data breach. And this is because only the bad news make the headlines. When there is a success story, when a company was able to avoid a data breach, when the tech team in the IT department stayed overnight to patch the servers and they were able to prevent a hack which would have happened in the morning, all that only means that nothing happens. I can guarantee to you that there won’t be a headline in your newspapers to our own morning saying that the biggest company in our country was not hacked yesterday.
Because that’s not news. When companies get hacked, it’s news when they don’t. And this means that the situation looks much worse than what it really is. The fact is that computer security has been getting better every year for 20 years. We have superior systems which are able to withstand the kind of attacks which would have wreaked havoc years ago. So we are getting better. Our systems are more secure than ever before. But we only see the bad news.
And I’ve sometimes described this as security tetris. In the game of tetris, with the blocks you’re trying to build a whole line. That’s what you’re trying to do. And when you succeed, the line disappears. So your successes disappear while your failures pile up. That’s exactly the same thing that’s happening in security. Our successes are invisible. They disappear. But our failures pile up. Cyber security tetris.
Are we spending money in the correct way?
Cybersecurity is expensive, but are we spending the money in the right place? This is a question that both governments and private sector are pondering about. And the answer isn’t easy. You see, the only way you can really know you’re spending your limited resources and you limited budgets in the right place is that you first have to do your threat assessments right. Different kinds of organizations are being targeted by different kinds of attacks because we have different kinds of attackers with different motives.
The risks that are faced by a defense contractor company are completely different from the risks faced by the chain of restaurants, for example. And they should be spending their money in different things. If you’re running a chain of pizza restaurants, you really shouldn’t be worrying about foreign governments, intelligence agencies trying to break into your network to steal your secrets. They’re not interested in your pizza recipes. But if you’re building missiles, that is a different story. And governments, ministries, decision makers, politicians, they do have to worry about the most complex and most expensive attack.
Some of the mobile phone attacks that we’ve seen recently are able to target, for example, iPhones. And people are worried about attacks like that. And I always comfort them with the fact that a targeted attack targeting your iPhone is possible. But it costs the attacker tens of thousands or hundreds of thousands of euros or dollars. And then the question becomes, are you worth targeting with an attack? And the answer for most of us is no. The answer to the prime minister or the big CEO would be yes. So it’s the threat assessment. What are you and your organization being targeted with sets the rules on where you should be spending your money?
Connectivity during crisis
During this war, I’ve had a number of meetings with Ukrainians, over Zoom, over teams, over Google meets. Now, whenever I’m in these meetings, I’m always astonished by the fact that I’m having full HD flawless video connection to a country which is at war. Sure, Ukraine has lost some of their national bandwidth during the war, but for most practical purposes, it’s very much online, even though Russia has been trying to cut them off. Now, there are many reasons explaining this, including the fact that they have a very large amount of local operators and the fact that they’ve been building new connectivity to West instead of the old connectivity and fiber optic cables that used to have through Russia and Belarus.
But I think the single largest explanation is the heroic work being done by the Ukrainian telecom technicians who are actually in the battlefield fixing cabling as it cuts by bombs dropping on top of them, risking their lives to keep the nation online. And that shows just how important connectivity is during crisis. That’s how we in the West see Zelensky’s speeches, how we see what’s really happening in the battle with how we see the atrocities. That’s how important it is.
Critical infrastructure privately owned
How should countries and governments defend themselves in the cyber space? Well it’s kind of complicated and one of the reasons why it’s complicated is that infrastructure, especially critical infrastructure has been slowly but surely moving into the hands of the private sector, critical infrastructure like power distribution and water distribution and food and transportation, which is good, but it makes it complicated for governments to coordinate and secure the critical infrastructure that runs our countries. In order to do that, we need cooperation, we need public-private partnerships.
And I think Finland is a pretty good example of the kind of public-private partnerships which actually work. In my view, companies, especially large companies, understand really well how important it is to do cooperation, how to exchange information with your peers and how to get ready for different kinds of crises. Not just conflict, but other kinds of crises as well. Why do we do it like that over here in Finland? Well there’s several reasons. I guess the most important being that we have a very big neighbor which we’ve had problems many times in history, but also the fact that, well, we have mandatory draft, which means very big part of the leaders in our companies have gone through military service, which gives them a different viewpoint. And that brings some sort of sense of togetherness and cooperation, which works. So public-private cooperation works and it gets great results. And really it is the only way to make sure that our countries and our societies are safe because companies run the infrastructure that runs our countries.
What would you build with no limits
I’ve been thinking about the future a lot lately since I’ve been writing a book about the future of technology. And one thing seems obvious to me, if you look at the long-term developments, connectivity has been becoming better, we have wider bandwidth all the time, we have more computing power, more memory, more storage, and it’s getting cheaper and cheaper and cheaper. This trend will continue, so where will it end? Well, I believe that eventually we will be living in a world where technology is practically limitless. As a computer user, as a programmer, as a builder, you will have access to systems with no limits. Think about this. Unlimited computing capability. Unlimited amount of memory. Unlimited storage for free. I’m not saying it’s literally. It’s not going to be literally unlimited for literally free, but it’s going to be closed. So close that it doesn’t matter anymore. And this is a very liberating thought. You can imagine that as a builder, as a programmer, you would have access to the biggest possible cloud instance imaginable with no limits and it’s going to cost you practically nothing at all. And then the question becomes, what would you build if there would be no limits?
Limited devices
lately I’ve been paying attention that many companies are issuing Chromebooks and iPads to their employees instead of giving out MacBooks and Windows laptops which used to be the knob. What’s happening here? Limited devices have better security. This is easy to see when you look at some other kinds of computers. For example, games consoles, play stations and Xboxies are obviously computers but you never hear about hacked Xboxies or PlayStations infected by malware. It’s not a thing because these are limited computers which are only able to do one thing. Xbox runs Windows but it can’t get infected by normal Windows malware because you can only run code published by Microsoft in the Xbox Store and exactly in the same way. Our iPhones, our iPads and Chromebooks and to some extent Android’s are closed exactly in the same way, making them much more secure but also much more limited. And this is the reason why companies are embracing these more limited devices to get better security and better manageability.
Power of open source
The most important Finn who has ever lived is not a poet or an architect or a scientist or a composer. No. He’s a programmer, Linus Torvalds. He’s still living today and he is the most important thing ever, easily. You see, he’s the guy who created the most popular operating system on the planet. Well, actually now, not just on this planet, you have Linux systems running even in Mars. And also the fact that he didn’t just create an operating system, Linux, he also created Git, which is again massively important development system for building the infrastructure around us. But it’s more than just this product. It’s the idea of open source, which really has been changing the technology world over the last 20 years. The idea that the programs we run can be modified by anyone. We can build them together instead of closed source systems built by specific companies, we have open source, which is free in all senses of the word. Open source does have its own problems. Open source systems are, if they’re successful, they will have users all over the world in all kinds of environments. And they might still be maintained by a small group of hobbies to don’t get paid for their work. And this easily translates into security problems. And we’ve seen this over the last years, over and over again, critical vulnerabilities in encryption systems or administration systems or while sharing systems.
What is the solution here? This is a supply chain problem. Supply chain for your programming environment almost always involves open source systems. And we can demand security and service from hobbies to don’t get paid for building these systems. If you want better security, you must maintain the security by yourself. You do the audits or you order the audits. You donate money to these projects to make sure they have the resources to build these systems better. Open source works. It is changing the world for the better, but you can’t just demand services for free.
Real attacks
There’s been many surprises in the war between Russia and Ukraine. From my point of view, the biggest surprise is how well Ukraine has been able to defend themselves against cyber attacks. In fact, I think Ukraine is the best country in Europe in defending their systems against Russian governmental cyber attacks, better than Germany, better than United Kingdom, better than the Nordics. Why? Because they’ve been defending against real attacks for eight years. All the other countries are playing war games and rehearsing make-believe table of exercises. Ukraine has been doing this for real for years. That’s what makes them best in defending against these attacks and its shows.




























