
 Interviewed by Hak5 tech show’s Shannon Morse, the legendary former hacker Kevin Mitnick unveils exciting facts of his intricate and captivating life story.
Interviewed by Hak5 tech show’s Shannon Morse, the legendary former hacker Kevin Mitnick unveils exciting facts of his intricate and captivating life story.
Shannon Morse: Today I am so excited to have Kevin Mitnick in this studio. Now, Kevin, you are known as the world’s greatest, most wanted hacker. So I have a question. Can you really hack NORAD1 and fire off missiles?
Kevin Mitnick: Well, you know, if I told you I’d have to kill you, but I don’t want to do that. But I’ve been practicing and I understand you guys might play the secret whistling codes at the end of your show.
– We might.
– Ok, I mean, you might want to keep it a secret, because you don’t want to give it to all the guys out there that might launch a missile or something. Yeah, but that’s true; I ended up in solitary confinement for 8 months, because what had happened was at one point I was arrested and I ended up in court. I figured I was going to get out on bail, my family was there. And then the prosecutor starts telling the judge: “Not only do we have to detain Mr. Mitnick, but we have to make sure he can’t get access to a telephone. Because if he does, Your Honor, he can pick up the phone, call NORAD, whistle the tones and possibly launch a nuclear weapon.”
– Oh my gosh, that’s hilarious.
– And when this guy said it, I laughed in open court because it’s so ridiculous.
– Was NORAD even online through the telephones at the time?
– I have no idea, I never had looked. So the judge actually made it an order that they had to ensure, when I was detained, that I didn’t have access to a phone, so the only place that they could put me was solitary; that was for 8 and a half long months.
– That’s horrible. I mean, you’re not the kind of person I would generally think of seeing in solitary confinement.
– No, it’s usually, like, when you kill a prison guard, kill another inmate, you know, you’re the Mexican mafia.
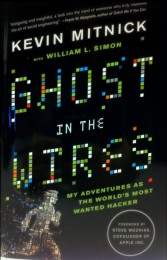
– I don’t think you’re mafia, right? Ok. So, Kevin, you wrote this book called ‘Ghost in the Wires’. I’ve read it and I thought it was incredibly awesome. It’s like a sci-fi thriller. But for anybody who hasn’t read it: what is it about?
– Well, it’s kind of about me and my adventures as a hacker from when I was a 12 year-old. My first hack was hacking the bus system in Los Angeles. There were no computers at the time, and I remember as a young kid I was riding on the back of the bus. And in Los Angeles at the time they would give you a transfer if you paid an extra dime. It was this piece of paper, and it had the driver-punched holes, meaning what bus line it was, what direction you were going. But it was a special punch. Every bus driver had unique shapes. You know, when you get free car wash after 10 washes – that type of thing.
– Oh, yeah, I have so many rewards codes for all the shopping that I do – trust me, I know about the hole punches.
– So, I was leaving the bus that day and I walked by the driver and said: “Hey, sir,” he goes: “Yes,” – “I’m 12,” and then I go: “I’m working on this project for school and we have to punch these special shapes on cardboard, and that punch is really cool, where do you guys buy them?”
– What kind of project would a 12 year-old be doing?
– I don’t know, I made it up on the fly, because I wanted to get the answer.
– It was totally innocent, so he believed you?
– He believed me; he told me the name of the store. I borrowed $15 from my Mom – and I go get the punch. But then the problem was: where do you get the transfers? So, as a kid I was thinking: “How do these guys drive a bus for 8 hours a day? They’re probably not going to clean the bus.” Probably some maintenance guys do it and throw everything in the garbage. So I rode my bike over to the bus depot, and this was my first experience with dumpster diving. It was out in the public area and I climbed over the dumpster, and I pulled myself over. It was like a jackpot. It was all these discarded books of transfers. And so I was riding around LA for free and I had no idea that what I was doing was wrong, because even when other people were waiting at the bus stop, I’d say: “Hey, I can punch you a transfer!” I used to punch transfers for people just sitting at the bus stop.
– That’s very kind of you to do that. That’s so nice!
– Yeah, a good Samaritan.
– So, you ended up going to jail for things that people thought you had done, and going through a ton of court, and you even ended up in solitary confinement at one point. That sounds like it would be really hard to share with the world. So, why did you write the book?
– A lot of people really didn’t know my story. There were 3 books written about me: ‘The Fugitive Game’, ‘Takedown’, ‘The Cyberthief and the Samurai’. And they all got it wrong. You know, they pretty much interviewed the police, interviewed people that were, like, former friends of mine and made up stories, like the NORAD story for example. And I thought it would be great to get out my story, because it was so interesting. And I spent my life kind of as a hacker, and I wanted to get the true story out – that’s really the reason. And they made a motion picture about me that wasn’t true, called ‘Takedown’. The movie sucked. Don’t go see it, it sucked.
– I kind of want to see it, just to laugh at it.
– It’s funny because I’m friends with one actress and one actor that played in the movie in real life now – Donal Logue and Angela Featherstone. But the movie was, like, horrid. I mean, what ended up happening is I was in jail, and my attorneys negotiated with the motion picture company Miramax and Dimension Films to do script changes and all this other stuff and pay me a financial settlement because it was liable.
– So, they didn’t really talk to you about the script or anything?
– No, they took it mostly from the book ‘Takedown’, which was untrue as well. So, how would you like that: you wake up one day and somebody’s making a movie about you that’s not true.
– It’s like “Hey, that looks awesome, but you got that part wrong, sorry”.
Shannon Morse: There were a whole lot of security flaws for a lot of corporates, a lot of companies that you write about in your book. Did you run into any kind of problems with those companies when you were writing the book?
Kevin Mitnick: No, because they don’t know about the book until they go read it. I mean, everything is 100% true, so I disclosed real names and real companies, and there’s no defamation in the book. So, as long as it’s true and it’s not under any type of protective order – I could write about it.
– That’s really surprising. I would have thought you’d have to go through a whole lot of legalities to be able to write some of the things in there.
– I had to go through more legalities on using pictures, when the pictures were taken by another party. I had to get signed releases, and I had to go through a lot of trouble, because in some of those pictures, I didn’t know who took them. Like, there was one of the guys named Justin Peterson, who was the government informant against me (using the handle ‘Eric Heinz’), and he was at SummerCon, and somebody else snapped the photo. So I found out who it was, and it took a long time. And especially one on screensavers: when I got off supervisor release they did a show, and I had to go because screensavers were the different companies, so I had to go to, like, Comcast and try to get them to legally release a picture, and it was like buying a house.
– So, was there anything that you couldn’t write about in the book? Like any kind of attacks that you wanted to talk about.
– Yeah, I can’t write about stuff that’s under protective order, because as part of my case the judge, because the government wanted it, put a protective order on stuff, the stuff I couldn’t talk about. But there were other hacks, because what actually happened is this book is 400 pages; I went way over word count. The book was only supposed to be 250-300. And my publisher was going to require me to take out a lot of the stuff, but they read it and loved it.
– Personally, I’m glad you included everything, because it’s interesting.
– One cool story is one of my social engineering, one of my favorite ones. This is like a rewind back to, like, 1984. I was in digital equipment corporation’s network. Their network was like my Disneyland, and I wanted to be able to sniff packets on the protocol called DECnet. And so this one company in San Fernando Valley, where I actually lived, developed a monitor sniffer tool for DECnet. So I wanted to get a copy. And I found out these guys ran their business out of a residence – that was, like, 2 guys. And they had a Vex computer and I was thinking: “How can I hack into it?” Because when I got the dial-up number and when I dialed up, it asked for system password. So there’s no way I’m going to be able to con them that way. So, what I did is I got an update tape from DEC, repackaged it and put, basically, a Trojan on the update tape, repackaged it up, shrinkwrapped it, put it in this box, and then I got a UPS uniform from a Hollywood shop.
– Oh yeah, those are so easy to find.
– I put on a hat, uniform, took a clipboard, and around 7 in the morning I knocked on the door, the guy answers. I woke him up, which was intentional – and I said: “UPS delivery, please sign,” and I was pushing myself into the door, and the reason why is: what do you think I didn’t have that would give me a way?
– An ID?
– UPS truck. No truck. So it took about 7 to 10 days.
– So, you didn’t buy a truck?
– No, I couldn’t afford it. I was, like, 18-19 years old. So, what happened is eventually, after about a week or 10 days they installed the update and I got in. But that was kind of cool because it was physical, it was kind of ‘James Bond-ish’ to me; it was kind of, like, you know: “Could I really pull it off?”
– That sounds actually really fun. So, were you worried about writing any of the different exploits you included here?
– No, I had to take a lot of technical exploits out, the reason being we wanted the book to be available to the general public.
– I noticed that. You made it really easy to understand a lot of more technical hacking aspects that you included in it.
– Yeah, like with .rhosts, which doesn’t really exist these days, but that I was able to explain and then I had different attacks, because, as it worked out, when one attack really works well, you just use it multiple times, it gets multiple targets. So, if you have a zero-day in Windows RPC, or in Apache, or RIS, you’re not going to sit there and try to use a different exploit for each target. You only use the same one over and over. So in a lot of the stories I used them differently. And then I illustrated it, and it becomes a fun read, because it’s calling up somebody over the phone pretending to be the help desk, saying that somebody reported a problem creating files with the period. I said: “Did you report it?”, and this guy, this engineer goes: “No, but can we try it out?” And I say: “Do you have .rhosts file?” And the guy goes: “No, what’s that?” I said: “Ok, let’s try creating one.” So he is creating a file that basically allows me into his system, and I say: “Ok, it works, so I’m going to cancel the trouble and now you can remove the file.” So it was all these different types of ways of using the social engineering and technical hacks to get in.
Shannon Morse: Speaking of people that you might have social-engineered, and same with the people that might have accused you of things: did you worry about any of the people that you had written about in the book? Like, did any of them confront you or anything like that?
Kevin Mitnick: Well, one did. I was working for this lady named Elaine Hill at a law firm, and that was when I was a fugitive in Denver. She was one of my bosses, so she wrote me on LinkedIn. She goes: “Hi Eric/Kevin,” because I was under the name Eric Weiss, the real name for Harry Houdini at the time. And she goes: “My husband is loving your book,” and, by the way, because I characterized her as a school teacher personality. And she goes: “You’re not going to believe what I do today,” and she told me that she’s now a school teacher, she goes: “You got me right!”
– It’s so cute! You had a lot of people that had lied to get you in trouble. Now that the book is out, did any of those people come up to you and say: “Hey, I’m sorry for saying that,” when they saw this book?
– No, not at all, none of my pals. My past hacking partner who was hacking with me for a number of years was Lewis De Payne. He’s not happy about the book, because I wrote that he cooperated with the government, but he wanted to clarify with me that he was cooperating after my sentencing so it would have no effect on me. So he was not really an informant. He was kind of disappointed that I wrote about him in that way, but I just tried to be 100% frank and honest.
– Ok, so you had so many fun hacks, it just sounds like you had such a good time doing it.
– It was kind of a game, but then again, it got more serious, because my goal was to become the best at circumventing security.
– You never made a dime off of any of these?
– It wasn’t money; again, it was seduction of adventure, curiosity, and challenge.
– So you never even wanted to make any money?
– No, I wanted to be the Harry Houdini of hacking. So I went after the source code of operating systems like VMS at the time and hacked it, and took a copy of the source code, which is, you know, a serious offence. I was leveraging that source code to become better at hacking, because I could analyze it for bugs, I could look at developer comments, I could change the code and patch system binaries. And then, when I eventually became a fugitive, I hacked into cell phone companies to get the source code so I could maintain invisibility.
And I knew it was important to maintain invisibility because when the FBI was chasing me, I was doing counter-intelligence: I hacked into the cell phone company in Los Angeles called ‘Pactel Cellular’, and there was this informant that was trying to set me up. So, what I did is I was able to get access to the call detail records, so I searched for who calls this guy, who in ‘Pactel Cellular’ calls this informant. And then I came up with a list of numbers, and I looked at their billing records, and it turned out that they were calling FBI internal numbers.
It doesn’t take a rocket scientist to figure out they’re the feds. So, common sense, I should have stopped there; but I didn’t have any common sense. I had this device called the DDI – the digital data interceptor, which allows me to monitor a cell site on the data channel and see who registers and see who gets calls. So I programmed these numbers into this device at my office – I worked as a private investigator. And I just let it sit there. And then, like, a month later I walk into the office and I hear: “beep, beep, beep”; I’m walking all around the offices – it’s coming from mine. What the hell is going on? I look at my computer, and I see my FBI early warning system has been trapped.
And it turns out that one of the agents – yeah, I was petrified – had called the payphone number, and I knew that number, what it was, it was the payphone across the street from the apartment I was living at. So I was thinking: “That happened 2 hours earlier, I was sleeping; if the FBI had come to arrest me, they would have walked in and they wouldn’t follow a hacker.” Why would they follow me? They already know where I work. So the next logical thing is they were going to do a search. In America, they have to get a description of the premises.
So, that night – I knew they were probably going to search the next day – I moved out all my computer equipment, my floppy disks. So I moved all that stuff out, and then the next day nothing happened, so I got a little bit bolder. I went to Winchell’s Donuts, I got a big box of 12 donuts and I wrote “FBI donuts” on it. I put it in the fridge, and then on a post-it note I wrote “FBI Donuts Inside” – like the “Intel Inside”.
And what happened is they raided me at 6 a.m. the next day, and the only thing they found were the FBI donuts. That’s why they were mad at me. And they didn’t touch any, I don’t know why; they left them all for me. Maybe they thought they were poisoned or something.
– Personally, I don’t think the law quite understands what it took to be a hacker back then. Do you think they would understand better now and maybe give you more fair treatment?
– Well, computers and hacking was kind of mysterious. And they couldn’t understand the non-profit motive back then. Today we’re post 9/11, so they probably would have treated me worse. Who knows? But to be locked up in solitary confinement on some myth that you could launch nuclear weapons? You know, who really knows? I was kind of the guy they wanted to make the example, to set an example for everybody else: “If you hack, this is what the federal government is going to do to you.”
And in fact, there was this guy named at Novell named Shawn Manley who I called up and convinced to set up an account on one of their terminal servers, and he asked me to call his voice mail to leave the password I wanted, and I did. He set up the account and I used it. But he never deleted that voice mail. And then, when they figured out what was going on, they turned that voice mail over to Novell security, it went to the San Jose police. But they played the recording, it’s just a voice, they don’t know who it is. So they couldn’t solve it. The San Jose computer crime squad had no idea who I was, I guess.
So, eventually it gets to the FBI in LA and one of the agents plays the tape, immediately knows my voice: “Oh, that’s Kevin,” calls up Novell, says: “I have some good news, I have some bad news. The good news is your hacker is Kevin Mitnick, the bad news is we don’t know where to find him.”
So, what eventually happened is when I was arrested and they held me for so many years without trial, this Shawn talked to the prosecutors, like: “What’s going on with the Mitnick case? How can you hold him for years without the trial?” And one of the prosecutors tells him, according to Shawn: “We’re going to teach him a lesson and send a message. And we know we’re violating his rights, but we don’t care”. Shawn was shocked, so he called my defense lawyer, offering to help me – and this is the guy I conned. We’re great friends today, I mean, we’re really good friends. He works for Fusion-io, and it was just like: “Wow,” he was appalled. And I didn’t even know what was going on, I was just sitting in prison, wondering where’s the light at the end of the tunnel. That’s a scary experience.
Shannon Morse: Given that this book is kind of a look at your past days and hacking, is there anything you regret from the past days?
Kevin Mitnick: Yeah, you know, I manipulated and conned a lot of people, that’s not cool, right? It’s not a nice thing to do, even though my objective was hacking. So I feel bad if I caused anyone to lose their job. Well, it’s not that I was a kid – I was doing this till I was 31. I don’t know if anyone lost their job, I don’t know what harm I caused to the individual. So I regret hurting anybody or causing any company’s loss, because to me cyber space was my playground, and I wasn’t trying to hurt somebody, I was just trying to be the Houdini of hackers.
– Now, how would you define black hats, and grey hats, and white hats? Is there any kind of line between them, and if there is, what place do you think you’re at?
– I don’t know who came up with that definition. I guess once you’re a black hat, you can never get that black out, right? So I’m probably grey, meaning that I did things illegally. I mean, where can you take an illegal activity, like computer hacking, and legitimize it? It’s really cool, because I do the same thing today: clients pay me a lot of money and I get to break into their systems, and it’s fun, and I help them. But it’s kind of like Pablo Escobar becoming a pharmacist, you know. I mean, where can this happen, right?

– That’s a terrible way to look at it. Now, what kind of techniques have you developed over the past years to hone your craft as kind of a social engineer?
– Well, I love Dave Kennedy’s social engineering toolkit. I mean, he’s taken that toolkit and made it easier, before it’s doing it by hand, using tools like Metasploit, it’s a fantastic tool, but a lot of it is: simply by having access to the tool doesn’t get you in. You have to really be meticulous at creating the situation where you’re going to get somebody to fall for it and not realize after they click or if they give you information over the phone that they made a mistake.
– You kind of have to be an actor, almost?
– Yeah, exactly, like one of the attacks in my book. This was actually a pentest, and what ended up happening is I bought an HP printer and created a CD, had somebody do the art and basically created drivers with a Trojan. I packaged it all up and called one of the executives at this company and told him I’m with the HP Early Adopter program: “We’d love to have you on the program, would you like a free printer?”
– And, of course, they’re not going to say no?
– They’re not going to say no, and I reminded them that it was very important because of debugging. I asked them what operating system they were using; it was Windows. If you’re using Windows, make sure you install the CD. He did it, and it’s coming up with the ideas, because the attacker wants to get software or malicious code on the box; usually that’s it. Like, all attacks today are using social engineering to drive a client-side exploit in Adobe Flash or in Office documents and stuff like that; or getting somebody to make a mistake, like plugging in the USB drive, installing a piece of software.
So you kind of think of a situation where somebody wants something, and it seems so reasonable. You open an HP printer and you see the CD, and it looks exactly like HP’s. You’re not looking at it for a counterfeit. That’s reasonable and it works. So, in both technical and social engineering pentesting that we’ve been doing since 2003 – we never failed. So, does that tell you that we’re really good or does that tell you security is really bad?
– In my opinion, security’s really bad.
– I agree. There is a lot of low-hanging fruit out there.
– Do you have any new projects coming up?
– Well, I finished my book. Right now we have a potential TV series – a huge network sent the book to the writers. It’s a shot in the dark – you know, that’s Hollywood. So, if the writers want to do it, then they’ll probably green-light a pilot, and we might have a TV series based on the book. I don’t know, I’m praying. So I’m really looking forward to that.
And I joined this company, it’s not announced yet, but this company develops Internet security awareness training about how you prevent social engineering in corporate environments. You have to simulate attacks on the users to inoculate them; it’s like having a flu shot – you don’t want to get the H1N1, so they give you a little bit of the virus so that your body builds that immunity. It’s the same psychological idea with social engineering: as you attack the users over a period of time, you inoculate them. Now, when the real attack comes, they reject it. So I just joined this company in an executive position to help create this product that will help companies prevent the future Kevin Mitnicks from getting in.
– Oh, the future Kevin Mitnicks, all the little 10 year-olds with the bus punch? So, for the 12 year-olds with a bus punch, the budding hackers, do you have any kind of best traits that you think they should have?
– Well, think fast on your feet. And, to me, hacking was all about the passion. It was just something I loved to do. I mean, it’s like sports: a guy who plays soccer goes out and practices 8 hours a day because he wants to be the best soccer player; well, I wanted to be the best hacker at circumventing security, because to me it was like magic. Because I actually started it, and I mentioned it in the ‘Ghost in the Wires’ that how I started hacking was wanting to perform magic tricks.
And then I met this kid in high school that could perform magic with the telephone: he was a phone phreaker. So I got involved in this hobby, and one to my first phone phreaker hacks – this was funny – was to change my friend’s home phone, another phone phreaker, to a payphone, so whenever he or his parents were trying to make a call, you know what they would hear? They’d hear this: “The call you have made requires a 10-cent deposit. Please hang up momentarily, listen for dial tone, deposit 10 cents and dial your call again.”
They hear this recording, my friend would call me: “Put it back, my parents are going to kill me!” So, what I did is I changed it into a prison phone so that they only can make collect calls. So I was just, like, playing with the system, I was a prankster.
– That’s so funny. So, if you could talk to your 12 year-old self now, what would you say to him?
– Wow! I mean, the world has changed from when I was 12. I mean, right now everybody has access to tools, like your favorite one is Metasploit; they have access to technology – this did not exist. You know, my first computer was in high school; it was an Olivetti terminal. A VT100 terminal and a modem would have cost you $3000-4000. It was unaffordable for me to learn about technology. So, what I used to do was roam through radio shacks in the San Fernando Valley and the college campuses, trying to hijack computer time so I could learn about technology.
Shannon Morse: Well, Kevin, right now we are going to have some awesome viewer questions for you. Alright, so the first one comes from Filipe. He asks: “What do you think about the recent hacking activities of groups like Anonymous and the release of classified documents on the web, like Wikileaks. And how would you contrast that to hacking back in the day?”
Kevin Mitnick: Well, it’s certainly a lot different from hacking back in the day. When I read about this stuff I go: “Wow, these guys have balls.” First of all, I look at Wikileaks; there wouldn’t be the Wikileaks without Bradley Manning. So, without Bradley Manning handing over all those documents, if he in fact did it, nobody would even known who they are. So, is it really Julian Assange, or is it Bradley Manning? That’s a question. But groups like Anonymous and especially LulzSec – it’s like “in your face”, right? “We’re going to do a DDoS attack against the CIA”, and today is “Fuck FBI Friday”, you know, and stuff like this. And I’m going: “I wonder how long it’s going to take before these guys are caught”.
And I’m looking at their Twitter feed – like, 300,000 people, and I’m looking at the times they tweet, you know, the type of language they’re using, and I kind of pinned it: I think these guys are in the UK, and eventually there were 2 guys arrested in the UK, they were leaders of the group. And it didn’t surprise me they were, like, 19-20 years old.
But the sophistication of their attacks – they’re using Low Orbit Ion Cannon to do server attacks – that’s stupid, because that’s doing a full TCP handshake, right? So there’s no way to spoof your source address – that’s when I’m thinking that’s kind of stupid. And then, more sophisticated users or members of Anonymous or LulzSec are really exploiting SQL injection. So, again, that goes to the answer: was I really that good or the security that bad? I think it really illustrates there’s a lot of low-hanging fruit out there, a tremendous amount. Look at Sony, what were they hacked – 22 times?
– I don’t even know. I stopped counting a long time ago.
– I bet their CSO is having a bad day. Of course it’s different, it’s subsidiaries that are being compromised, but it’s just like they went wild after Sony. I don’t know if that had to do with George Hotz and that whole suit against him for cracking the PS3, or if it was like: “Hey, this is a cool target.”
– Well, thank you Filipe. The second question comes from Nate, he says: “Who do you look up to?”
– Harry Houdini; Bruce Lee is one of my idols. I really look up to Steve Wozniak, because the guy is an amazing guy. He actually did the foreword of my book, which is amazing. I wasn’t expecting he would agree to it, but he did. Again, I like the spy type of genre; and, really, Harry Houdini, because I love magic still today; Bruce Lee, because he’s like the ninja in martial arts; and people like Woz, who are engineers and changed the world. I look up to people even like Steve Jobs; I never met the guy, but what he has created… in my pocket I have an mp3 player, I have an Internet browser and I have a telephone – all in one device. Without him being the captain of the ship I might not have that in my pocket.
– You might not have this laptop… yeah, same thing. Right, thank you Nate. The next question is from Andy, he says: “What are your views on the US Government laws like SOPA that limit our rights as citizens of the Internet?”
– It doesn’t surprise me, but it’s a law, from my understanding (I didn’t look at it in depth), that has no due process. If there’s now an infringement that the executive branch determines – they’re the judge and jury, and executioner – if they determine that something violates copyright, they can sit there and interfere. Basically, it stopped DNS resolution, and I think that’s terrible. As we learned, once we as Americans give up rights, like the Patriot Act, they’re forever gone, you never get them back.
What even surprised me, and I tweeted this the other day, is there was a law passed in Illinois, but I think it was recently reversed, where it was actually a felony to record the police. If you see a police officer beating a guy and you’re with your iPhone recording it – this guy was facing 75 years in prison. So I tweeted, I go: “This is proof that we’re actually in a police state.” Thank God, from what I understand, a judge stroke that down as unconstitutional, but just in that one state, doesn’t mean these other states won’t pass the same law. So someone has to get arrested, get a lawyer and, you know, jump through all those hoops.
– Let’s hope that doesn’t happen. Alright, the next question is from Jootsy. He says: “Kevin, in your book you describe your hacking as an addiction and it’s constantly your downfall and your savior. How would you describe the insatiable itch for hacking?”
– I’m still a hacker today, but to me it was like a complete passion. I don’t know if you can call it an addiction, or an obsession, or just passion, you know. I’m not a psychologist, but I just was compelled to do this because I loved it so much, and it drove me. Even today I do the same thing, except I do it with authorization and I get paid for it. But it’s still – I love hacking and pentesting, the only thing that is kind of the downside is I have to do a report. But that’s the deliverable. So you’re having fun figuring all these vulnerabilities in web apps, in people, in physical security, and then you have to write a very smart-looking professional report, and that’s kind of the work part, that’s like: “Ok, I’ve got to do the deliverable.”
– I guess it has to happen now and then. Alright, this one is from an anonymous entry; he says: “When you were a fugitive, what was the deciding factor for when to leave a place?”
– When I was a fugitive, if there was any sort of risk. My first place I went to was Denver, and in the book, in ‘Ghost in the Wires’, you’ll read that I actually was fired from my job at the law firm because they thought I was consulting on firm time because I’d always be on lunch on my cell phone – they didn’t realize I was running from the government and I wasn’t even paying for my cell phone calls.
And then I decided: well, it would be too risky to set up new identity in the same place, so I basically threw a dart… Well, I threw a dart and then I decided to look at Money Magazine to pick my new place. I would set up these early warning systems to be able to perceive a risk. Like when I was at the law firm, one of my jobs was supporting their telephone system for client matter billing. And so I put in some code into their system, that if anyone at their law firm called the FBI in Denver, or LA, or the US Attorney’s office in Denver and LA, it would send a message to my pager. So I had this early warning system, it tripped twice: I was freaking out but it turned out to be a false alarm – they were calling the civil division.
I always was one step forward – two steps back, or two steps forward – one step back. So I’d constantly be setting up these early warning systems, and if there was any time I should have stopped and got out, that was in Raleigh where I was eventually arrested. If destiny hadn’t taken me there, I probably would never be on this show, and maybe I’d be still living out there running.
– And then we would have never met. The next question is from anonymous ‘coward’: “War Games, the Net, or Hackers?”
– War games. Sneakers, I think it’s a really good one. And I want to see ‘The Girl with the Dragon Tattoo’ that come out, the Swedish film. I’m really excited to see the English version, too. You’ve got this hot chick hacker – ok, cool!
– Alright, I’d like to thank you so much for coming on this show!
– Thank you Shannon!





























One of the best things to happen to me in recent times is the contact of this amazing cyber guru I found. This man by the name Albert Vadim helped me comfortably read all my ex’s messages from my own phone. I could see WhatsApp messages, SMS, Snapchat and even access to phone calls. If not for this, I would have been completely broken because I was only being used as a means to get into America with a marriage certificate. My so called partner was married in another country with 2 kids. All thanks to Albert, I escaped this nightmare. You can reach out to Albert on EmaiI: Vadimwebhack@ gmaiI. com