
Security analysts mostly deal with ransomware attacks deployed through exploits, booby-trapped email attachments, or Microsoft Office loopholes occurring when users are tricked into enabling macros. A series of recent onslaughts, however, stand out from the crowd because the offenders have been taking advantage of TeamViewer sessions as the malware entry point.

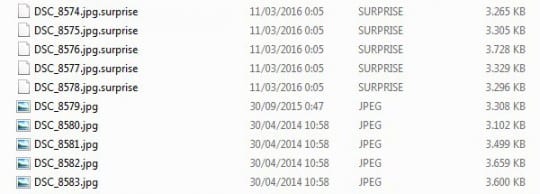
The ransomware campaign under consideration surfaced March 9 and originally didn’t seem to differ a lot from numerous copycats. One of the infected users started a thread at Bleeping Computer security forum, stating that his personal data, including images, videos, text documents, PDF and DWG files became inaccessible all of a sudden. An unknown malicious program had encrypted the files and concatenated a “.surprise” extension to every filename. Therefore, a sample item named “presentation.pdf” morphed into “presentation.pdf.surprise”.
In addition to that, the ransomware created several new files on the Desktop, namely DECRYPTION_HOWTO.Notepad, Encrypted_Files.Notepad, and surprise.exe. The first two are ransom notes and encrypted files list, respectively, and the last one is the malicious executable. The document with ransom instructions tells the victim to contact the hackers over the following emails: nowayout@protonmail.com and nowayout@sigaint.org, and provide such details as the country, computer name and username. The user should indicate the same information in messages to both of the above addresses, probably because the bad guys assume either of these accounts may be suspended as a result of infected people’s complaints.
The files can only be recovered if the victim pays a ransom in Bitcoins. Interestingly enough, the amount depends on how important the locked data is, and it may range from 0.5 BTC to as much as 25 BTC. These terms are to be negotiated individually. Obviously, if this ransom Trojan hits an enterprise network consisting of multiple machines, the ransom will be much higher than in a single PC assault scenario. The cybercriminals are also “kind” enough to decrypt one file for free, which is sort of a cold comfort to the target. This way, the black hats simply try to prove they are actually able to restore the frozen data.
As researchers started looking into the incident, they realized that it wasn’t a run-of-the-mill ransomware breed. The inspection of its executable – surprise.exe – revealed the Trojan’s affiliation with the ill-famed Eda2, a fully functional open-source ransomware devised by Utku Sen, a Turkish enthusiast who wanted to demonstrate how this sort of malicious code operates. The researcher ventured to publish his source code on GitHub. Although he emphasized that Eda2 was intended for educational purposes only, cybercriminals ended up using it to coin more than 20 real-world crypto malware spin-offs. This turn of events made Mr. Sen abandon his proof-of-concept project and remove the code from GitHub, but ransomware operators had apparently made copies to further use it for creating new file-encrypting viruses.
The surprise.exe process loads the malicious program from Base64 encoded string into the targeted computer’s memory and launches it from there. When deploying the crypto job, the malware ignores a number of directories, including Windows, Program Files and folders whose depth exceeds 235 characters. The Trojan uses a mix of RSA-2048 and AES-256 to encrypt files. The combination of public-key cryptography and symmetric cipher makes it impossible to derive decryption keys. The only viable recovery method is to access the criminals’ Command and Control server and try to obtain the keys stored on it, but the C2 appears to be down for the moment. Security examiners also found that this ransomware runs a batch script to erase Shadow Copies and thus make the VSS-based file restoration vector inefficient.

The main zest of this campaign, though, is in the way the ransomware propagates. It turned out that all infected users who joined the aforementioned forum thread had TeamViewer v10.0.47484 software installed on their computers. Moreover, the analysis of TeamViewer traffic logs showed that someone had remotely executed surprise.exe process on computers, which resulted in malware injection behind the scenes. Furthermore, the researchers discovered that the user ID was identical across most of the unauthorized remote connection sessions, but not all. It’s therefore premature to state for a fact that one account (479440875) was used to infect systems. The scariest thing is that the strange traffic behavior had been taking place for months in some of the reported cases.
Preliminary analysis of this incident has spawn some speculations regarding the role of TeamViewer in these attacks. There may have been an undetected breach that resulted in a massive theft of user credentials. Both the Bleeping Computer experts and infected users reached out to the vendor for comments on this defiant abuse of their service. In particular, identifying the likely attacker by the ID mentioned above might help stop the malware circulation and track down the perpetrators. No official response has been received from the company so far.
Meanwhile, the C2 for Surprise Ransomware remains down. This circumstance is a doubled-edged sword. On the one hand, the extortionists are unlikely to attack new workstations, because the secret encryption keys cannot be generated by the server, and decryption keys cannot be properly stored. On the other hand, the users who fell victim to this Trojan earlier have hardly any chances to get their files back even if they are willing to pay the ransom. The likelihood of forensic software recovering the data isn’t high either, because the infection leverages advanced shredding techniques to securely delete the original copies of one’s files.
The usefulness of TeamViewer is out of the question as the program has got remarkable functionality under the hood. And yet, the company should probably do a better job protecting their service from unsanctioned manipulations that may result in obfuscated malware deployment on a large scale.





























Thanks for the information. Any news of TeamViewer?
Javier,
Here’s what they have to say in an official statement regarding this issue, “Thus far we have no evidence that would suggest any potential security breach of TeamViewer that attackers exploit. … Careless use is at the bottom of the cases we currently looked at. This particularly includes the use of the same password across multiple user accounts with various suppliers.”