As the smart home technologies are booming to make people’s lives easier, it is more relevant than ever to question the security aspects of the IoT based model.
The Internet of Things has been the talk of the town this decade. Networks of connected devices are driving progress that people can literally touch and benefit from in the most tangible ways imaginable. In particular, the IoT evolution has brought about fundamental changes in the way our homes are built on the inside. Smart camera surveillance systems, TVs, baby monitors, fridges, thermostats, door locks and personal assistants aren’t attributes of science fiction screenplays anymore, having become the norm for millions of people around the world.
The traditional counterparts of some of these devices appear obsolete. For instance, the classic security cameras cannot be viewed from a smartphone, and run-of-the-mill door locks won’t open up remotely. With the whole indisputable convenience and advantages of IoT home entities in place, there is one huge caveat – they are all connected to the Internet. Everything that’s online is potentially exploitable by external threat actors who no longer need to do things like lock picking to intrude on people’s homes and privacy.
The bar of sophistication has been raised, but so has the level of the concomitant security concerns. Under the circumstances, the importance of home network security solutions that meet the new growing challenges is coming to the fore.
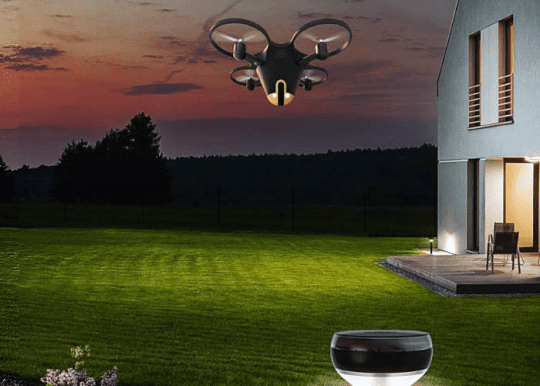
Some of the most exotic contrivances tailored to harden home security seem to hail from the future. Security drones hovering sentinel over your home make a good example. The ostensibly down-to-earth things like smart locks are becoming increasingly complex, too. Newer releases operate via fingerprints, touchscreens or Bluetooth, making the metal key an outdated phenomenon.
But what’s the flip side? Here’s a scenario providing some food for thought. By hacking your CCTV system, malefactors can easily learn when you are away. During your absence, they will come by and remotely invoke a command so that your previously breached smart environment system opens a window. And voila, they’re in doing their filthy job the old school way.
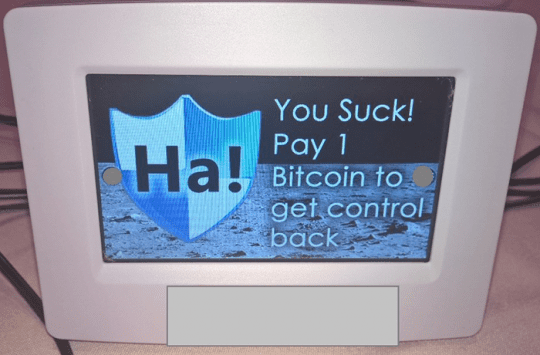
Of course you might argue that the manufacturers of such high-end intelligent devices take security seriously and won’t let that happen. Unfortunately, this is a misconception. These companies focus so heavily on invading their niche in this growing market and winning the competition that security isn’t one of their biggest priorities. The Internet of Things is crammed up with vulnerable firmware that sometimes cannot even be patched.
And yet, smart homes are steadily becoming ubiquitous. Essentially, each one resembles a mini corporate network and therefore needs adequate levels of security. A lot of people, though, aren’t willing to make their daily routine more complicated by, say, entering a password to turn on the toaster. In fact, this isn’t entirely a joke.
It’s not the super hi-tech drones, CCTV and smart locks that we should secure more effectively. More trivial things like the above-mentioned clever toasters, thermostats and fridges are the more likely targets. Since these devices operate within the same wireless network as the properly protected stuff, they make a perfect entry point for intruders. The home network is only as secure as its weakest link.
Analysts single out two main security issues with IoT devices that people keep in their homes. The first one comes down to overly high privileges. A bevy of these connected objects have more permissions than they really need. The more access, the broader the potential attack surface in the worst-case scenario. Another concern is that some of the built-in applications interact with the devices via unencrypted messages. A threat actor tampering with a home network can therefore intercept sensitive details, such as the passcode for the door lock.
One of the optimal ways to tackle most of these security and privacy risks is to use a specially crafted free IoT scanner. It can detect all the entities connected to your home network and stay on the lookout for anomalous activity. For example, it will alert you whenever somebody tries to connect or when one of your devices is attempting to establish a connection with a server it’s not supposed to reach.
Importantly, the security assistant will deploy vulnerability assessment to identify backdoors in your network. It typically also goes equipped with a safe browsing feature that keeps your devices from accessing unsafe websites. Other functions, such as parental controls, brute force protection and exploit prevention, add an extra layer of security to your smart home setup. All of these features are accessible via an app compatible with your mobile device. When properly configured, a tool like that can become a one-size-fits-all solution to safeguard your trendy home.