
Content:
A big trend of today’s cybercrime is distributing ransomware locking victims’ computers allegedly on behalf of local law enforcement agencies. One of such infections pretends to come from the Royal Canadian Mounted Police, a reputable Canadian national police service. While the name of this institution inspires undoubted trust, blocking PCs is definitely not on the list of their practices.
The malware to blame is called Reveton, which is a Trojan designed specifically to disable user access to the affected operating system. This virus is sophisticated enough to determine which country the infected machine is in, so that it gets the corresponding external manifestation. Numerous instances of contamination with this threat testify to the fact that some security software turns out incapable of intercepting the malicious thing. Moreover, infiltration proper may take place covertly through exploiting Java vulnerabilities and other out-of-date software’s flaws.
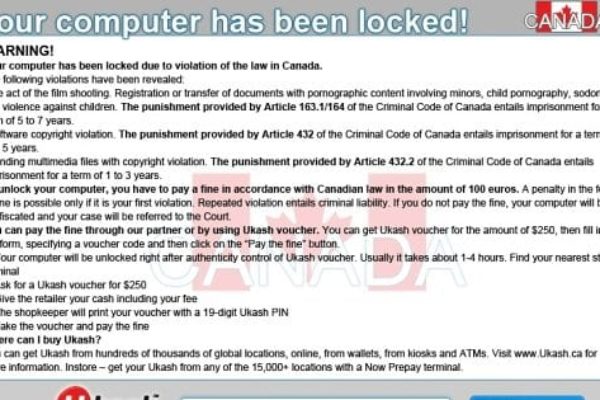
Having made it into the targeted system, Reveton displays a lock screen during Windows startup, stating that “the work of the computer has been suspended on the grounds of unauthorized cyberactivity”. The fabricated message also provides the specific laws that the user has purportedly violated, relating to Copyright violation, adult content distribution, promoting terrorism, cheating with payment cards, etc. According to the alert, the unlock routine implies submitting a code from a 100 CAD value Paysafecard or Ukash prepaid card which can be bought in a variety of places throughout the country.
Along with prevalently hitting Windows, this particular malicious code was found to be able to affect Mac OS as well. However, the latter instance is much less severe since it results in blocking Safari browser only, not the entire system access.
Our key advice here is to abstain from doing what the fraudsters ask – first off, because you didn’t actually violate anything, and secondly, because the lock screen is all fake. The rest of this article sheds light on details of this ransomware’s activity, and provides a comprehensive step-by-step cleanup method to help you combat and defeat the Royal Canadian Mounted Police (RCMP) virus for good.
Royal Canadian Mounted Police virus: versions and screenshots
There have been several updates to the lock screen generated by this malware. The pages do differ significantly in their design, yet the key idea remains unaltered: displaying a spooky alert that the PC has been locked, listing the laws that were supposedly violated, and demanding the victim to pay a 100 CAD fine via Ukash or Paysafecard. On Mac OS, the fake block page appears in all tabs opened in Safari browser. Below are images of the screens this ransomware was found to display.
RCMP ransomware: symptoms and dangers
- Fake lock screen on Windows:
During OS startup the Royal Canadian Mounted Police virus displays an alert page containing false information on the reasons for blocking. Bypassing this screen in the regular way is impossible: you cannot bring up the Task Manager, nor can you launch the rest of the applications. - Webcam control:
Some Windows-based variants of this virus gain access to the webcam (if any) on the infected computer, displaying a streaming video from it. The scammers are obviously hoping that the aspect of being ‘watched’ will induce the victim more into pay the fine. On Mac OS this is not the case. - Blocking Safari on Mac OS:
Mac users are a little luckier in terms of the infection symptoms because the RCMP ransomware only blocks the web browser while allowing the use of other applications. The phony web page appearing in every tab says that all your files have been encrypted “to prevent their distribution and use”. Another good news here is that the Mac variant is much easier to get rid of – we will show you how in one of the sections below.
Royal Canadian Mounted Police virus removal
Due to peculiarities of this malware, standard cleanup through launching security software installed on the affected computer is not applicable. Likewise, manual removal is considerably aggravated because of inability to access system directories where the virus embeds its components.
Having thoroughly analyzed this piece of malicious code, we came up with a number of removal methods that proved to work in terms of complete extermination of the RCMP Ukash/Paysafecard virus.
Royal Canadian Mounted Police virus removal using HitmanPro.Kickstart
For performing this removal procedure, you will need a USB drive to further launch the cleanup software from. Please note that all the data on this USB drive will be lost, so make sure you back it up before proceeding.
- Download HitmanPro software to a computer that is not affected by the virus and save it to your Desktop. Before performing the download, be sure to select the version according to the bit-type of your Windows operating system (32- or 64-bit).
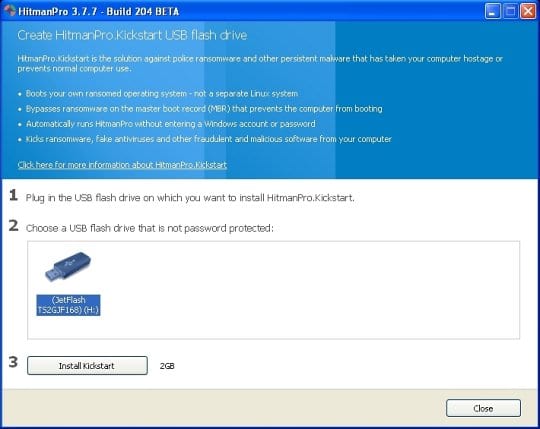
- Plug in the USB drive that you are going to use for installing HitmanPro.Kickstart. Having inserted the thumb drive, double-click on the HitmanPro icon on your Desktop. The program’s main Window will appear. Please click on the kicker button as indicated by the red arrow on the screenshot below.
-
You will now see a window that will guide you all the way through creating the HitmanPro.Kickstart USB flash drive. Select the right USB drive by clicking on it in the corresponding field, and click the Install Kickstart button.
The software will ask you whether the USB drive contains any important files (all of them will be erased). If there are none, click Yes on the alert. This will automatically initiate the install process. When it completes, click Close button. - Remove the USB drive and insert it into the computer infected with the RCMP ransom virus.
-
When it is inserted, turn off the infested PC and switch it back on. As the computer is beginning launch, take a good look at the boot screen to find the key that should be pressed for accessing the Boot Menu or BIOS Setup. Please note that these keys may be different on different computer models. For entering the Boot Menu, those are mainly F10, F11, F12 or Esc buttons. The ones for BIOS Setup are usually Del or F2.
Having determined the appropriate key for Boot Menu access, reboot and start hitting that key repeatedly as the PC is beginning to load. When in the Boot Menu, use its prompts to select the drive you want to boot your computer from, i.e. USB drive. -
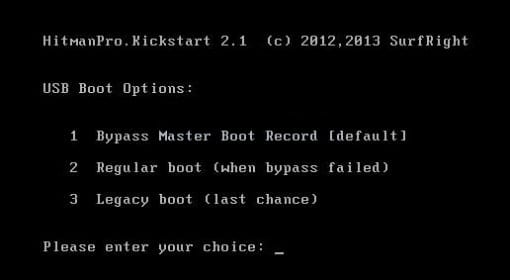
Now your PC will boot from the USB drive and load the HitmanPro.Kickstart saved to the memory stick. You will see a screen requesting you to choose USB Boot Options.
You should press 1 as your choice. Doing so will be followed by Windows starting to load. -
Right after Windows launches, the fake Royal Canadian Mounted Police block screen will appear as it did before, however in 15-20 seconds the HitmanPro main console will pop up on top of that.
Please click Next on the program’s GUI. -
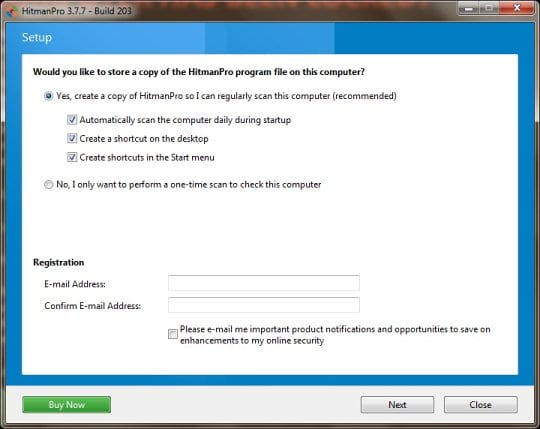
On HitmanPro’s setup screen that appears, we recommend leaving the default installation settings as shown on the following screenshot:
Please click Next.




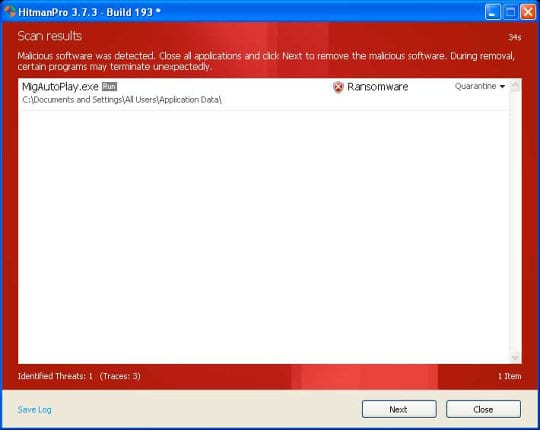
- SurfRight HitmanPro will now start a virus scan. Having completed the scan, the utility will come up with a report listing the detected threats.
- To get the spotted infections eliminated from your system, click Next. After the removal routine is complete, choose the Reboot option on the subsequent screen. Your computer will restart as usual. The Royal Canadian Mounted Police virus is no longer affecting your system. If you are not certain your current antivirus can prevent such threats from infiltrating your system in the future, you might want to consider upgrading to HitmanPro licensed version.
Royal Canadian Mounted Police virus removal using System Restore
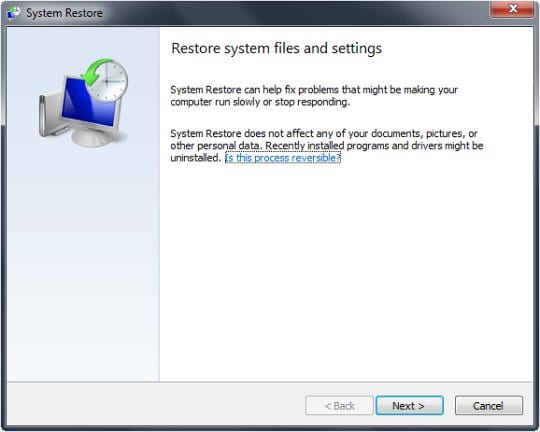
This cleanup method allows restoring your operating system to the time period when it was not contaminated with the RCMP ransomware. This procedure will not lead to loss of any files. To perform system restore, please stick to the following steps:
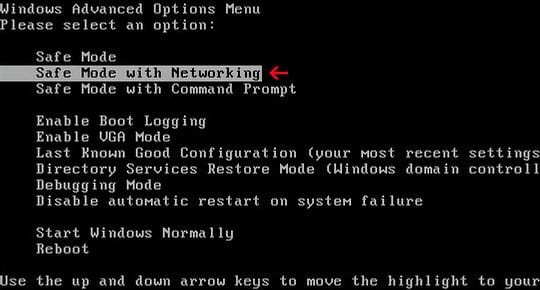
- When the infected computer is starting to load, tap F8 on your keyboard repeatedly to open up Windows Advanced Options Menu. When on this screen, use the arrow keys to highlight Safe Mode with Command Prompt, and hit Enter.
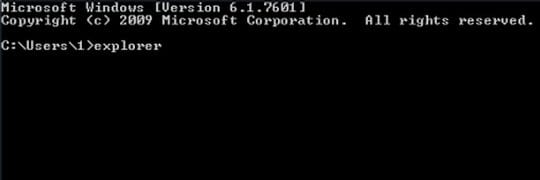
- Once the Command Prompt screen opens, type explorer and press Enter. Be advised this needs to be done quickly (within 2-3 seconds) or else the malware will not allow you to type anymore and you will have to start the process over.
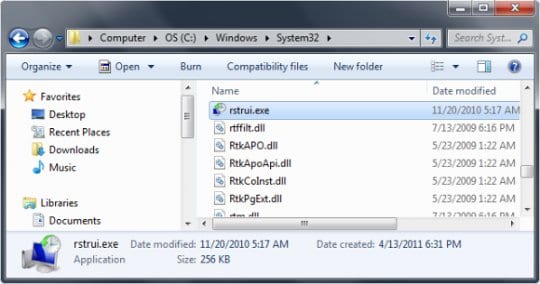
- In Windows Explorer, browse to the following path:
On Windows XP: C:\windows\system32\restore\rstrui.exe and hit Enter
On Windows Vista / 7: C:\windows\system32\rstrui.exe and hit Enter
- Using the System Restore prompts, get your system restored to the date when it was unaffected by the malware.
Download, install and run reliable security software to get effective protection from cyber threats further on.

Royal Canadian Mounted Police virus removal from Mac OS
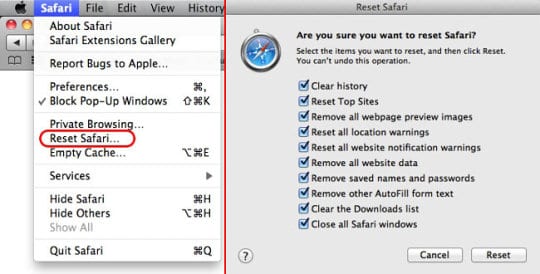
All you need to do in order to eliminate the RCMP ransomware from your Mac computer is resetting the browser which has been affected. Click on the Safari button in the upper left-hand corner of the browser and proceed to the Reset Safari… option. Make sure all items are checked in the corresponding window, and hit Reset.
Now you’re done. With all the benefits of this method, i.e. its effectiveness and simplicity, there is a drawback which consists in the fact that all of your saved passwords, browsing history, list of downloads, etc. will vanish. However, this will assure that you won’t suffer from the consequences of the Royal Canadian Mounted Police virus any longer.


































Thank you so much, I thought my computer was dead. Everytime I booted up my computer it would shut down. For anyone unsure about feeling it maybe to difficult, it was pretty easy to follow the directions that privacypc.com laid out. If you want to save your computer, use this site!
Thanks,
BAM